Purism patches Meltdown and Spectre variant 2, both included in all new Librem laptops
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
Purism has released a patch for Meltdown (CVE-2017-5754, aka variant 3) as part of PureOS, and includes this latest PureOS image as part of all new Librem laptop shipments. Purism is also providing a microcode update for Intel processors to address Spectre variant 2 (CVE-2017-5715).
Securing an existing PureOS installation
Applying the patch for Meltdown
Running Software Update will upgrade PureOS to include the linux-kernel package and associated dependencies to the 4.14.12 patched version.
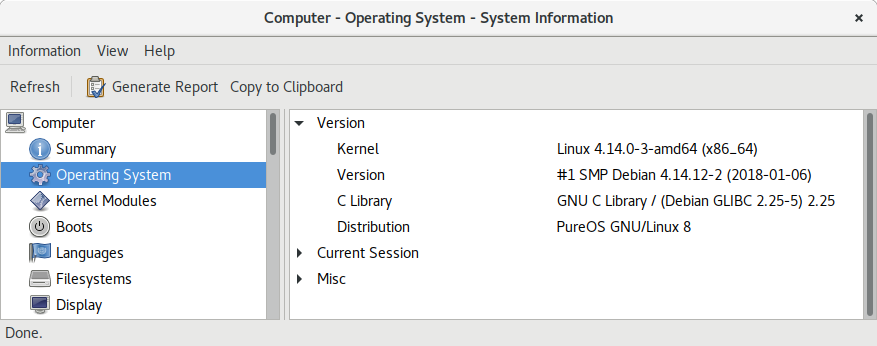
This update will require a reboot to apply, after which you should see that you are running 4.14.12. You can use the uname command to check:
user@librem-13v2:~$ uname -a
Linux librem-13v2 4.14.0-3-amd64 #1 SMP Debian 4.14.12-2 (2018-01-06) x86_64 GNU/Linux
Applying the patch for Spectre
Unfortunately, at the moment, patching Spectre variant 2 requires applying a proprietary CPU microcode update from Intel. Since PureOS contains only free software, this means that Purism customers owning Librem laptops will need to add a new repository from Purism (completely independent of the PureOS software repositories) to download and apply this microcode update.
First, create a file called /etc/apt/sources.list.d/purism.list that contains the following lines:
# non-free Purism repo for microcode deb http://deb.wp.puri.sm/pureos/ green contrib non-free
You will need root permissions to edit this file so if you would like to do this with a graphical editor hit Alt-F2 and type: sudo gedit /etc/apt/sources.list.d/purism.list or if you want to use a text editor in a terminal type sudo nano /etc/apt/sources.list.d/purism.list (no text editor holy wars please!)
Then, add the Purism repository key to your APT keyring:
wget -O - https://deb.wp.puri.sm/pureos/key/purism-nonfre-repo.gpg.key | sudo apt-key add -
Once you have added the key, use apt-key finger to verify that you have the following key, and that its fingerprint matches:
$ apt-key finger
...
pub rsa4096 2018-01-14 [SC] [expires: 2028-01-12]
CC2B 0E61 FE48 7DCD 96FA 632C 64CD 8D1B DE94 49B1
uid [ unknown] Purism non-free package repository (Signing key for the Purism non-free repository for PureOS) <deb@deb.wp.puri.sm>Then use apt to install the intel-microcode package:
$ sudo apt update $ sudo apt install intel-microcode
Version 20180108.1 or newer contains the patch for Spectre variant 2. Like with the Meltdown patch, this will require a reboot to take effect.
New installations are secured
Downloadable PureOS installation images have been updated accordingly, and anyone downloading and installing the latest images will be protected against Meltdown. If you reinstall PureOS, you will still need to perform the above steps in the “Applying the Patch for Spectre” section as PureOS doesn’t include the non-free Intel microcode package.
As for Purism customers, all new laptop shipments include Meltdown and Spectre patches, as they will have the latest PureOS image (that includes the Meltdown patch) preloaded and will also have the Spectre variant 2 patch applied. All existing Purism customers will need to follow the above steps to make sure they are protected against both Meltdown and Spectre variant 2.
Recent Posts
Related Content
- Landfall: A Case Study in Commercial Spyware
- Code is Power!
- Purism Approach vs. Google Model
- Spotify “Panama” Leak Is a Wake-Up Call for Digital Privacy
- Google Mishandling School Children’s Data


