Your Own Personal Enclave: The Smart Card Reader on the Librem 5 and Liberty Phone
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
There are many unique features in the Librem 5 and Liberty Phone that make it stand out when compared to other smartphones. The easily-accessible hardware kill switches with lockdown mode, removable WiFi and cellular modules, and the fact it uses the same PureOS operating system as our laptops get the most attention. These are great examples of how Purism approaches innovation differently from most tech companies. We favor open standards and build solutions that put the user in control, not us. While that’s often meant we’ve had to avoid proprietary off-the-shelf solutions and do things ourselves, in other cases it’s meant using existing tried-and-true open technologies like OpenPGP smart card readers in a new way–as a secure enclave fully in the user’s control.
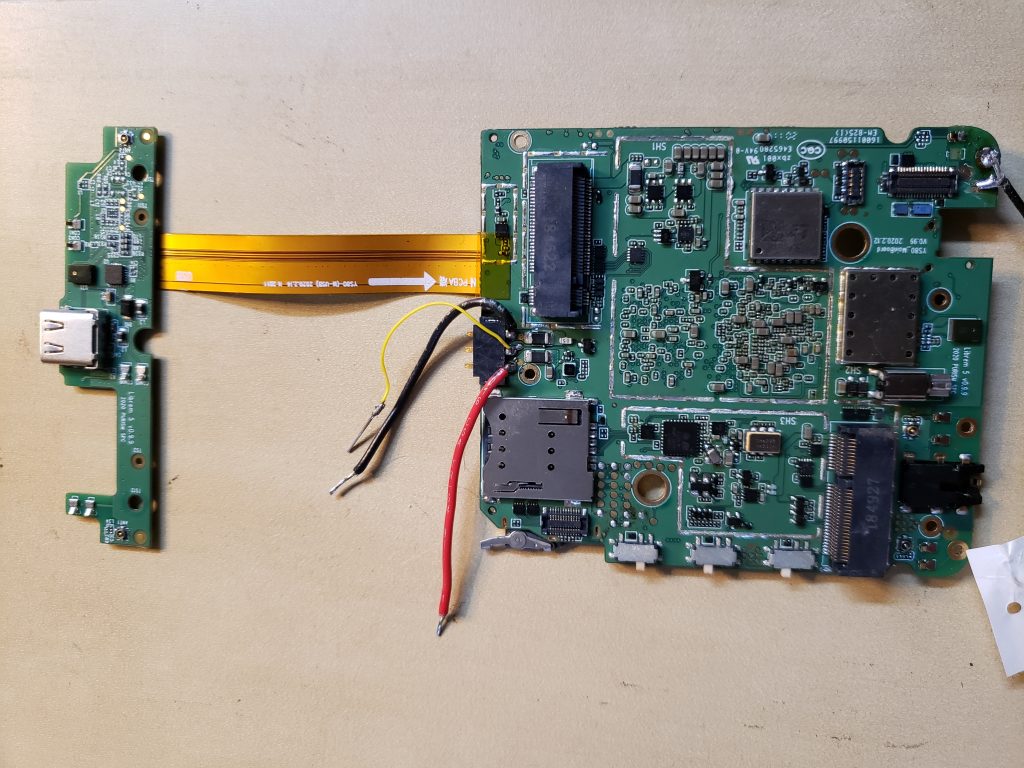
We recently got the smart card reader functioning on our Librem 5 Dogwood batch and I realized we haven’t talked much yet about the smart card reader. In this post I will discuss why we decided to add an OpenPGP smart card reader to our phones and how we intend to use it.
What’s Smart About Smart Cards?
Smart cards are ubiquitous technology. You can find them in everything from modern credit cards to USB security tokens like our Librem Key. The idea behind smart cards is to have a discrete and tamper-resistant chip that can store secrets securely and perform a set of cryptographic operations using those secrets without having to expose the secrets outside of the smart card. Data goes in, the smart card uses its secrets to manipulate that data, and modified data goes out.

In the case of an OpenPGP smart card, the secrets you store are private GPG subkeys like you might use to encrypt or decrypt email or files, or sign code you are contributing to. While you can store GPG keys on your local hard drive (and many people do), storing them on an OpenPGP smart card (such as on a USB security token like the Librem Key) adds a few extra layers of security.
The first layer of security a smart card adds is by preventing keys from being copied. Once a private key is copied onto a smart card, it can never be copied back out. If an attacker were to compromise your computer, they could make copies of your GPG private keys in your ~/.gnupg directory on their own computer and attempt to brute force the password. If they were able to guess the password you used to secure those keys, they could use the keys to sign and decrypt things on your behalf on their own computer. Yet if those keys were on a smart card and the smart card were inserted the most they could do is sign and encrypt/decrypt things on your behalf while they had access to the computer–and only if they could guess your PIN. They couldn’t make copies of the key and use it elsewhere and the moment you removed your key from the computer they would no longer have access.
The second layer of security a smart card adds is that it performs cryptographic operations with your keys on the smart card itself. Your private keys are never copied into system RAM even temporarily.
Finally, a smart card becomes an authentication factor referred to as “something you have” like a physical key or an identification card (a password is “something you know”). The portable nature of smart cards means that you can keep them with you at all times and since they can only be in one place at a time, they can prove that the user has possession of authentic secrets.
Why Put a Smart Card In a Smart Phone?
While desktop and laptop computers sometimes have smart card readers, and there are a number of specialized handheld devices used for point of sale and other functions that contain smart card readers, to our knowledge the Librem 5 is the only smartphone to have one. We recognized the value of smart cards for storing secrets securely when we developed our Librem Key for use with our laptops. Since a person’s phone arguably stores even more sensitive information than their computer, we felt it was important that it have some way to protect that information with strong secrets on a tamper-resistant chip.
Smart Card or Secure Enclave?
Phones need a way to protect against attackers who might root the device and extract cryptographic secrets from RAM and many phones today that solve that problem with a discrete chip known as a secure enclave. The chip behaves in many ways like a smart card in that it stores secrets and has a set of cryptographic operations it can perform but these chips are permanently soldered onto the PCB.
Along with any user secrets secure enclaves also tend to store certificates provided by the vendor. This is because in addition to handling your secrets securely, they also enforce the vendor’s secure boot and software verification system. By storing these certificates in the secure enclave they can make sure that you only run authorized firmware, software, and even can only attach authorized 3rd party hardware to the device. The reason you see secure enclave chips on modern smartphones has more to do with enforcing vendor control over the hardware and software and less to do with protecting your own secrets.
When we set about to solve the problem of secret storage on the Librem 5, we decided against a permanent secure enclave chip in favor of a smart card reader for a few reasons:
- While there are exceptions, many secure enclave implementations are closed hardware that run proprietary firmware.
- We believe users should own their own hardware so we weren’t interested in technology that risked removing control from the user.
- Smart card readers are well-understood, ubiquitous and open technology with free software implementations.
- Smart cards are removable and replaceable by the owner at any time and are relatively inexpensive to replace.
So you can think of a removable smart card like your own personal secure enclave fully under your control.
Librem 5 Smart Card Use Cases
Having an integrated smart card reader in the Librem 5 opens up all sorts of possibilities. Here are a few of the use cases we are already working toward with the Librem 5.
Secure GPG Key Storage
The obvious first use case for a smart card is to provide the owner a secure place to store their GPG keys. While you can already do this with some other smart cards it requires you to store keys on a separate USB security token with Near Field Communication (NFC) capabilities. On other smart phones whenever you want to perform GPG operations you have to take out your security token and hold it up to the phone. While that is a secure workflow, it’s also somewhat inconvenient–especially if you use GPG frequently. Our approach combines the convenience of storing your GPG keys on the local file system with the security of storing them on a smart card.
Simple Disk Unlocking
We intend for the Librem 5 to feature disk encryption for the root disk and at the moment all of the standard tools are there like you would have on any Linux computer. The one missing bit left to be developed is software we can fit inside the initrd file to allow the owner to enter their disk unlock passphrase on the touchscreen since unlike a normal Linux computer the Librem 5 doesn’t have a physical keyboard.
On our laptops we already have mechanisms within PureOS that allow you to unlock your disk with GPG keys on a Librem Key. Once configured, you get prompted for your GPG PIN at boot and the smart card decrypts a GPG-encrypted file that contains the LUKS disk unlock secret. After we complete the software to allow passphrase entry on the Librem 5 touchscreen at boot, it will be simple to add the ability to unlock with your GPG keys instead.
Secure Authentication
GPG provides three different classes of subkey you can store on a smart card. The first type of key is for encryption, the second is for signing and the third is for authentication. The authentication subkey is often not created and isn’t in wide use, but it’s something you can use for secure authentication for services such as SSH and there are already plugins in place to allow this kind of functionality. This would mean you could store SSH authentication secrets safely on your smart card and SSH from your Librem 5 to remote machines without risking that your SSH private key might be copied and reused by an attacker.
General-Purpose Secret Protection
We can also take advantage of the smart card to provide a general method to protect other secrets on the device by encrypting them with your GPG keys stored on the smart card. You might use this not only to encrypt local files or entire removable SD cards, but you could also use it to protect a local password vault or other sensitive files.
Recoverable Secrets
Given so much can depend on the secrets stored on a smart card, it’s important that you be able to backup and restore it in case a smart card chip fails or is lost. Because the smart card is removable and it uses standard GPG keys, you can use the same standard methods to backup and restore GPG private keys like you would with a laptop and a Librem Key. If a secure enclave chip fails you are out of luck, but because the smart card is not only removable, it is relatively inexpensive, you can easily create a backup smart card when you first set your keys up and store it in a safe place along with a thumb drive that contains your full set of private keys.
User Personas
The workflow I’m most excited about with smart cards on the Librem 5 is the idea of user personas. You can configure the Librem 5 so that all of the things that make up a person’s unique identity on the Librem 5 are removable: the cellular modem (IMEI), the cellular SIM card (IMSI), the WiFi card (MAC address), the microSD card (personal files and settings), and the smart card (user secrets).
A common problem people have with their smartphone is how to handle their sensitive data when they travel. When you travel you are not only more likely to lose your phone or have it be stolen, you also risk a customs official searching through or even copying your data as you cross a border. While some people have come up with elaborate steganography or safe word approaches to attempt to smuggle data across borders, the most secure approach is one where you travel only with data you can afford to lose such that you can fully comply with any customs agent requests. This is where user personas come in.
If you think of a user persona like a traditional user on a Linux system you can imagine a scenario where that user’s home directory is stored on a removable microSD card and secured with GPG keys on a smart card. You can then get a different pair of microSD cards and smart cards for each user persona you want to set up.
For instance you might have a “normal” persona that contains your personal contact list, personal social media account secrets, your personal calendar, work files and similar information. All of these files, settings and secrets would be protected by GPG keys on a smart card. To set up a new persona you could then store (or backup) all of that information on a microSD card and wipe that user account clean.
Travel Persona
For travel you can then create a “travel” persona that contains only the files, accounts, contacts, and calendar entries you need for your trip. These files and settings can be protected with a different set of GPG keys you have stored on a separate smart card. Then if your phone gets lost or stolen or if a customs agent searches it, the only files and settings that are at risk are the ones you explicitly need for travel. If you want to go an extra step you could even swap out the cellular modem (for instance if you are a US citizen traveling to Europe you might swap the US version of our cellular modem for the EU version so you have access to more European cellular frequencies). Then when you arrive you can get a local prepaid SIM and be on your way with a completely compartmentalized travel persona. When you return from your trip you can swap back in your personal microSD card and smart card and restore your personal persona.
Conclusion
I hope now that you are as excited as I am about the possibilities an integrated smart card reader gives you with the Librem 5. We constantly aim to balance your freedom, security and privacy and develop solutions that provide you not only with strong security, but also full control over your own hardware. We feel the OpenPGP smart card reader in the Librem 5 is another example of a strong but open security method that puts all the keys in your hands.
Recent Posts
Related Content
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence
- PureOS Crimson Development Report: March 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale
- PureOS Crimson Development Report: January and February 2026 – Beta Released
- Privacy Under Siege


