Apple Has No Tolerance For Webcam Covers
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
We sell laptops and phones with hardware kill switches at Purism, so we clearly have strong opinions about webcam security. It shouldn’t come as a surprise that we raised an eyebrow when Apple posted an update to their support page titled “Don’t close your MacBook, MacBook Air, or MacBook Pro with a cover over the camera” where they advise against using a webcam cover on MacBooks because:
If you close your Mac notebook with a camera cover installed, you might damage your display because the clearance between the display and keyboard is designed to very tight tolerances. Covering the built-in camera might also interfere with the ambient light sensor and prevent features like automatic brightness and True Tone from working. As an alternative to a camera cover, use the camera indicator light to determine if your camera is active, and decide which apps can use your camera in System Preferences.
This support page addition was picked up in the media and as some media outlets have reported, apparently enough customers have damaged their screen by closing it with a webcam cover that the issue justified this public guidance.
On one hand it’s encouraging to see that enough people are concerned about their privacy, and webcam covers are so ubiquitous, that it’s an issue worthy of its own support page. What’s discouraging is Apple’s security advice on the issue, which is to rely on MacOS webcam software permissions to restrict what apps can access the webcam and combine that with a hard-wired green LED that should always turn on when the webcam is in use. While this advice is consistent with Apple’s overall “just trust us” approach to security, it completely misses the point of why people used webcam covers to begin with: to claw back the tiniest bit of control over their privacy from hardware and software companies.
It’s this issue of control that I want to discuss in this post. Apple and Purism take completely different approaches to security. Apple’s approach is to require customers to hand over all trust and control to Apple and depend upon Apple for all of their security. Purism’s approach is to give customers control over their own computers and provide security without depending upon Purism. Webcam security is a great lens through which to view these completely opposite approaches.
Why Webcam Security Matters
Before I discuss different webcam security measures, it’s worth talking about why webcam security is such a big deal to begin with and why so many people ranging from privacy advocates to executives of billion-dollar companies started covering their webcams. The simple answer is the prevalence of Remote Access Trojan (RAT) software that grants an attacker access to a computer over the Internet including control of its webcam and microphone. Many people leave their laptops open at a desk, table or nightstand which means their camera is aimed into their room. Someone who could install a RAT on your computer might then be able to grab compromising pictures or video of you in addition to any files they might be able to steal. This software spawned an entire creepy underground community of “ratters” where people share nude pictures of victims and tips on how best to use RATs for extortion. Webcam security has even been dramatized into a disturbing Hollywood thriller.
What has been especially troubling with RATs is the fact that attackers are able to watch and record people through their webcams without their knowing. For the longest time people assumed that their webcam was only on if the LED was on. Unfortunately webcam LEDs are controlled by software so the RATs simply modified the software to leave the LED off.
Since the computer, its software, and the webcam LED couldn’t be trusted, many privacy advocates resorted to covering their webcams with everything from tape to bandages to Post-it notes. At first people who did this were dismissed as paranoid but eventually this has become a common enough practice that webcam covers have even become popular swag at conferences. While webcam covers don’t protect against someone snooping on you with your microphone, if you don’t have a Purism computer with a hardware kill switch it’s the next best way for a person to take control over their own privacy without having to rely on their laptop vendor.
Apple: Just Trust Us
Apple has responded to webcam security concerns by putting it more firmly in their control. First on the software side they have set up webcam permissions similar to what you’d see on a phone. Applications must request permission before the OS allows them to use the webcam. For this approach to work, you must fully trust Apple and the security of the software behind these controls. If an attacker can bypass this software like RATs have done in the past, or if they could convince a user to grant permissions to an app, the attacker could still spy on you through your webcam. Alternatively, an attacker can compromise an application that already has access to the camera, like happened last year with a major Zoom security flaw on Macs.
Apple’s second approach is on the hardware side. On past laptops they had the same software-controlled webcam LED as other vendors. On recent laptops they have hardwired the webcam LED so that it turns on whenever the webcam receives power. To protect your privacy with this kind of security measure you must check the webcam whenever you walk past your computer and make sure the green LED isn’t on. Beyond that you are left hoping that the LED won’t turn on when you aren’t there to see it. If the LED does turn on, you might know that some program is using the webcam, but other than shutting the laptop lid, you don’t have much control–after all you might damage the laptop if you cover up the webcam!
The fundamental flaw with Apple’s approach is that it takes all control over security and privacy away from you. To be secure you must fully trust Apple and their security measures and if anything ever happens to violate that trust, such as a security exploit, there isn’t much you can do about it.
Purism: You Are In Control
We approach security from a completely different standpoint than most security companies. If you were to ask most security engineers to design a security measure, they would inevitably come up with a system that requires you to delegate all trust and control to them. This would also conveniently make you dependent on their company and product for your security.
I have written in the past about how with Purism products, you are in control. When we design a security measure we start from a standpoint of giving you the maximum amount of control over your own computer without having to hand over trust to Purism. When we looked into how to solve the problem of webcam security, we opted for a simple but powerful approach in the form of hardware kill switches. With hardware kill switches, you can completely remove power from the webcam and microphone just by flipping a switch. This puts you in complete control over your own privacy as you can leave the webcam and microphone off most of the time and only turn it on when you actually need to use the hardware. Since it’s a convenient switch, you aren’t left fumbling through software settings buried inside of a program.
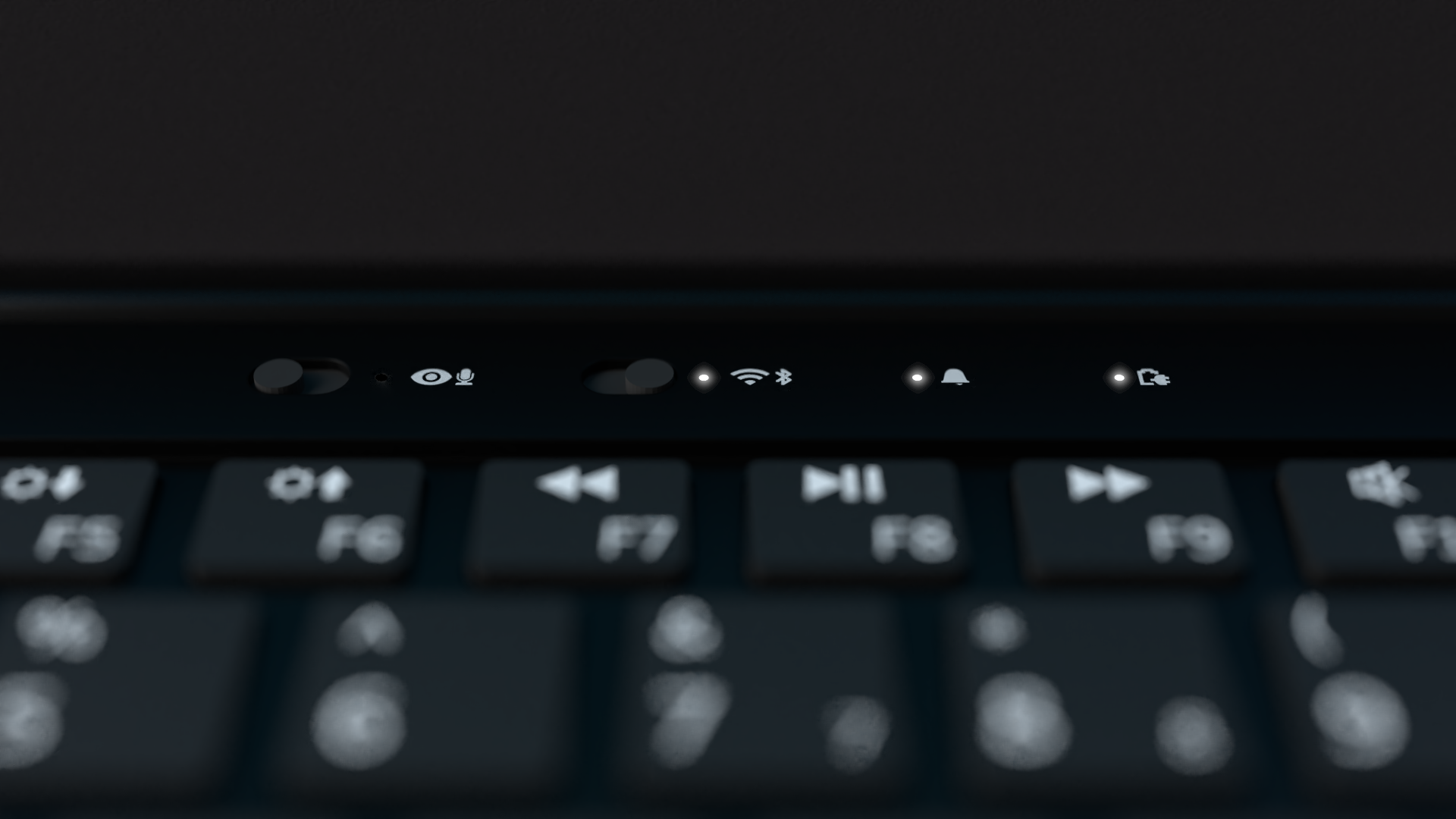
Webcam Privacy On Your Phone

When we designed our Librem 5 phone from scratch, we made sure to add and expand our hardware kill switches to that hardware. With the Librem 5 you can control your cameras and microphone, WiFi and Bluetooth, and even the cellular modem with kill switches. You can also flip all of the switches and enable “lockdown mode” to disable all sensors on the device.
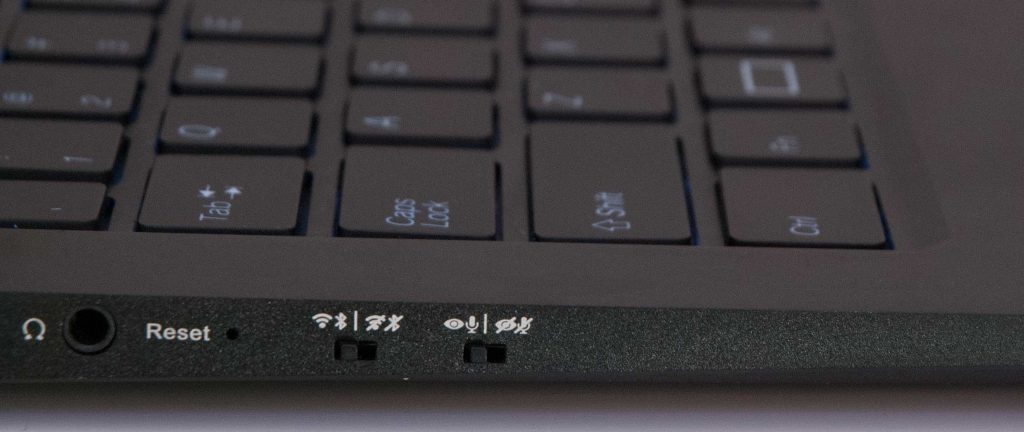
Kill Switch Improvements on the Librem 14
With the Librem 14 we went back to the drawing board to design our dream laptop and in addition to many other improvements we revisited how we implement hardware kill switches. For starters we moved the kill switches from the side of the laptop back above the keyboard and added an LED. This not only solves the problem of switches getting flipped accidentally when you put the laptop into a backpack or sleeve, it also allows you to audit the state of the switches quickly without craning your neck to the side of the laptop. I’ve found myself forgetting I left the webcam on after a video call so I’m looking forward to the new-and-improved kill switch location.
Switch How You Protect Your Privacy
In the end, your privacy and your computer should belong to you, not the vendor that sold it. If you want real privacy, it’s not enough to entrust it to someone else, especially when that requires you to trust software that no one can audit. As last year’s Zoom flaw shows, even if you do trust your laptop vendor, you could still lose your privacy from a bug in third-party software. Instead of giving up control in exchange for privacy, switch to products that respect your privacy and your control.
Recent Posts
Related Content
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence
- PureOS Crimson Development Report: March 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale
- PureOS Crimson Development Report: January and February 2026 – Beta Released
- Privacy Under Siege


