PureBoot 101 | First Boot, First Update, and Detecting Software Tampering
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
Whether you face serious threats or just want peace of mind, PureBoot lets you detect tampering starting from your boot firmware down into the OS itself.
The PureBoot bundle is comprised of the BIOS, Librem Key, and USB vault. This video dives into what each part does.
This next video shows you what to expect when you first receive your PureBoot bundle, how to handle updates, and what it looks like to detect tampering.
The Key
The Librem Key is a small USB device that handles encryption and detects tampering on your computer. While we ship with unique keys preloaded for each PureBoot bundle, you can reset these to your own keys and secrets at any time.
While we ship with unique keys preloaded for each PureBoot bundle, you can reset these to your own keys and secrets at any time.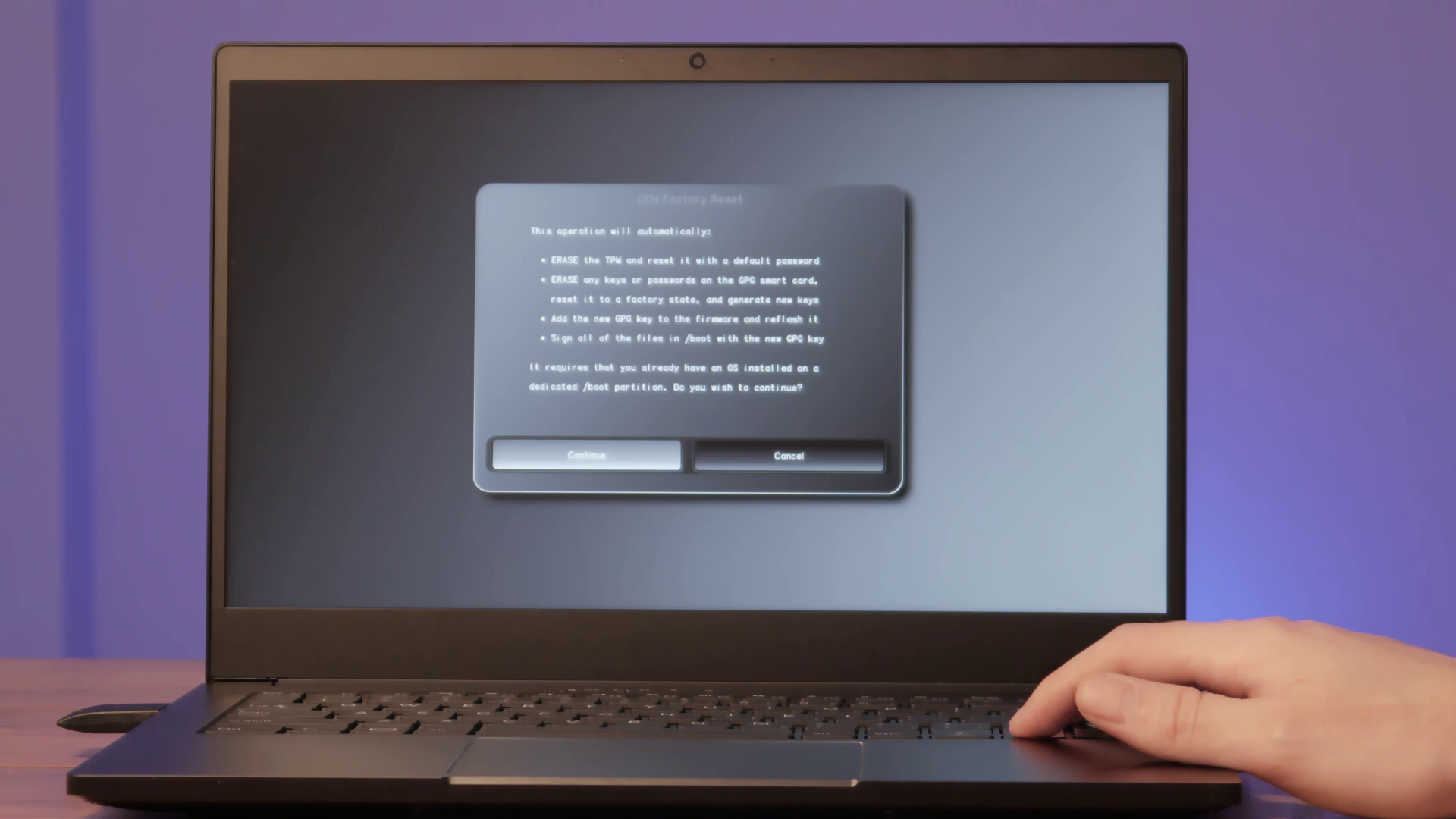 When you attach The Librem Key to your computer on startup, PureBoot proves to the Librem Key that it hasn’t been tampered with. If it can, the Librem Key blinks green.
When you attach The Librem Key to your computer on startup, PureBoot proves to the Librem Key that it hasn’t been tampered with. If it can, the Librem Key blinks green. Once you can trust PureBoot itself, it verifies the Linux kernel and other files in /boot have not been altered before you boot into your OS.
Once you can trust PureBoot itself, it verifies the Linux kernel and other files in /boot have not been altered before you boot into your OS.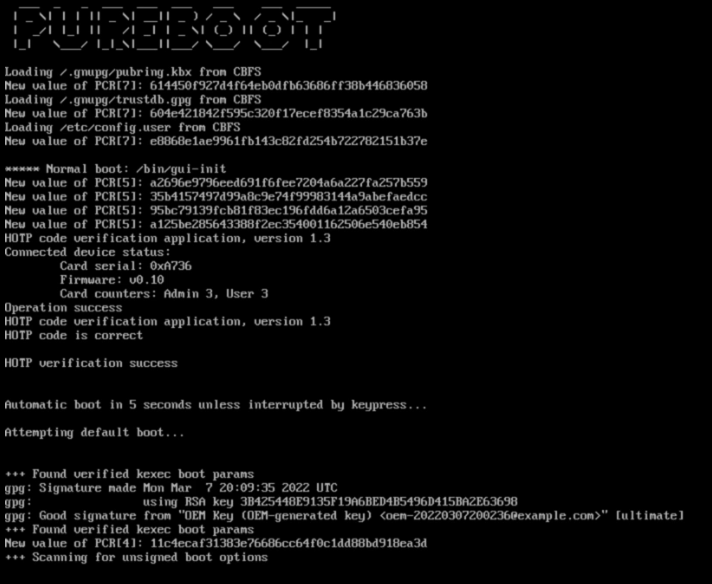
The BIOS
At a basic level, PureBoot is a lot like Secure Boot. In a nutshell, both PureBoot and Secure Boot use advanced cryptography to verify the OS is valid. The big difference is who decides what software is safe. With PureBoot, you are the one holding all the keys, not Purism or another vendor.
PureBoot is free software and runs from a tiny Linux environment.
The tools PureBoot packs in allow you to verify your boot files are the same as you left them or troubleshoot why they aren’t and gives you many more recovery options than a traditional BIOS.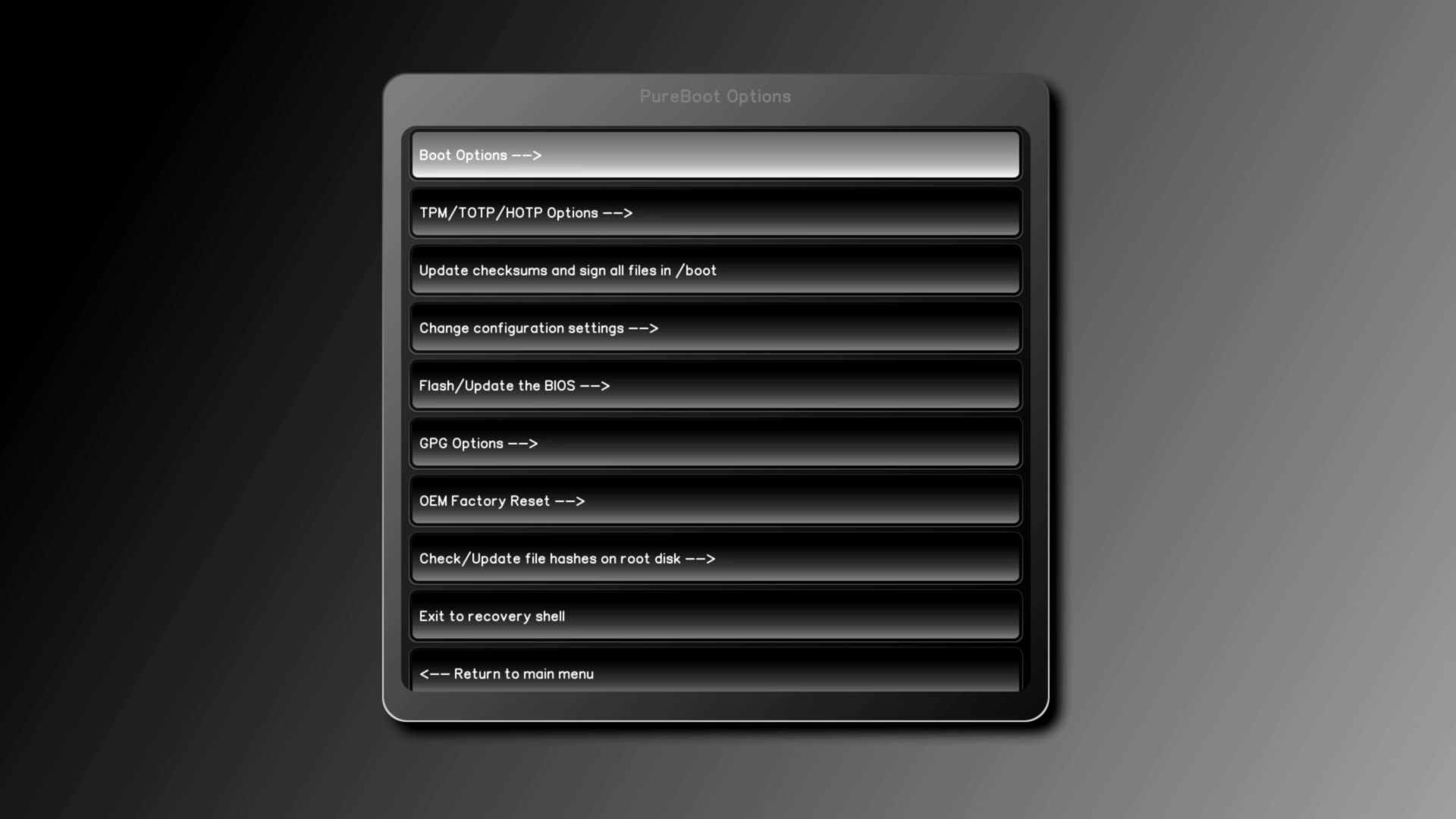
The USB Vault
The PureBoot bundle also comes with a USB Vault. Stored in the Vault is a copy of your Librem Key’s public key. This key can be used to encrypt data that requires the private key to decrypt.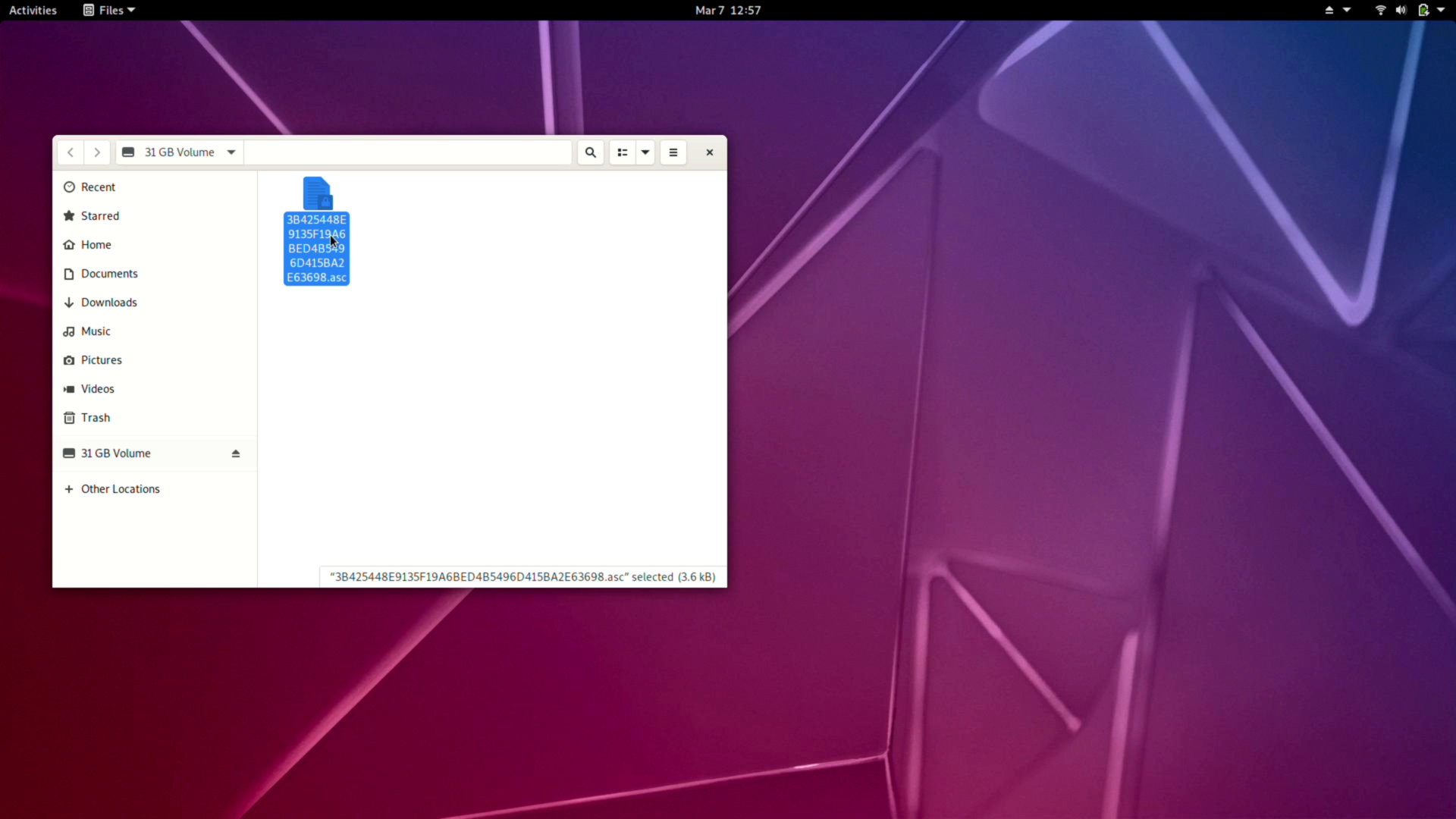 This matching private key only exists on the Librem Key and cannot be exported.
This matching private key only exists on the Librem Key and cannot be exported. The public key is helpful if you ever need to reconnect your Librem Key with the BIOS without resetting your private key.
The public key is helpful if you ever need to reconnect your Librem Key with the BIOS without resetting your private key.
To make copies of a Librem key, you would need to generate new keys and copy them onto the individual Librem Keys. Following this guide or the below video, you can backup the resulting keys in your password manager and keep them on your physical Vault USB locked away in a safe place.
First Boot
Once everything is unboxed, attach your Librem Key and power on your Librem device. The Librem Key will quickly blink a few times while it is being detected, then slowly flash red or green, depending on the verification check. 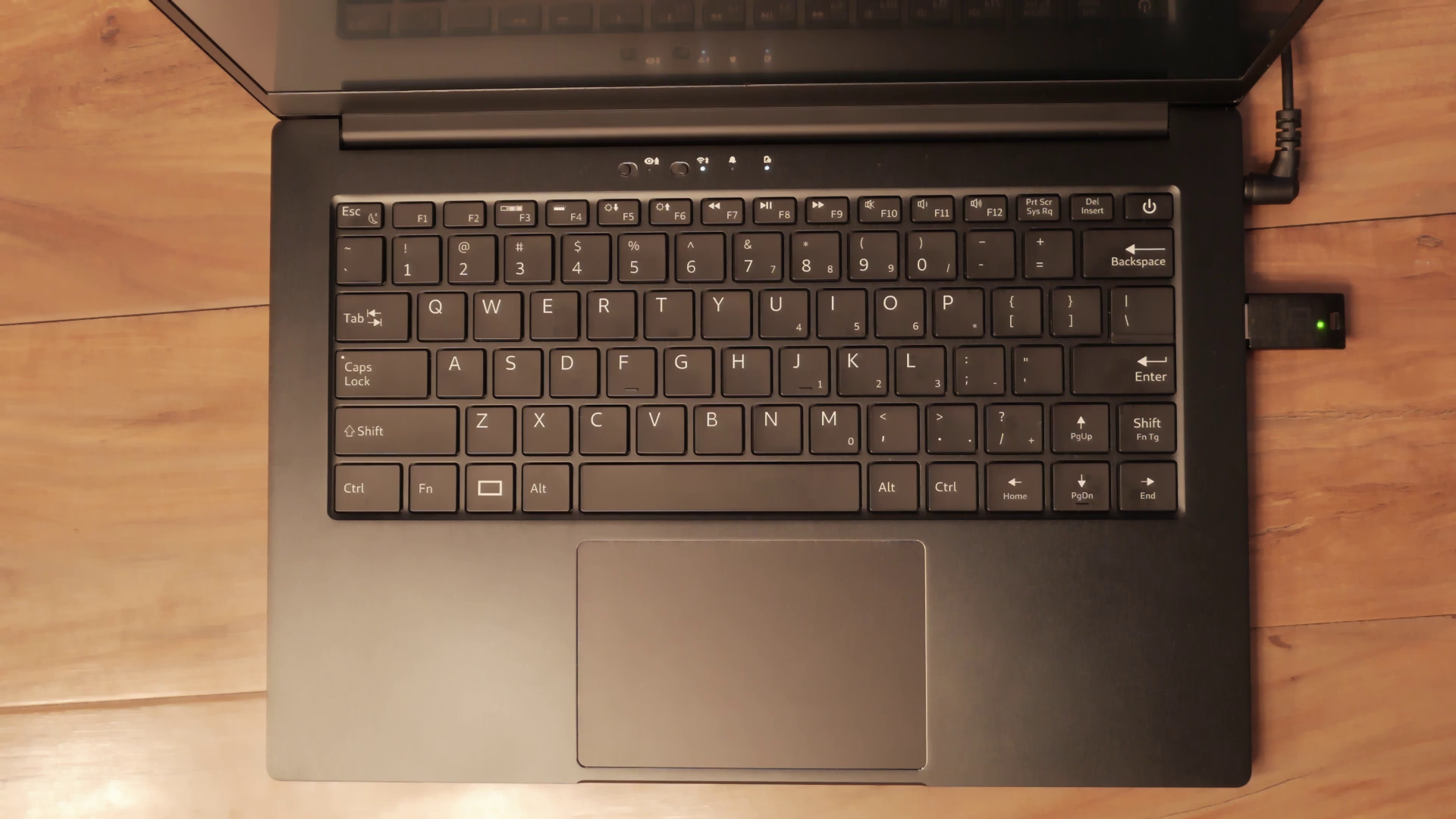 When it blinks green, it passed the boot check, and the boot firmware can be trusted. Then it checks that all /boot files are unmodified before it automatically boots into the OS. This should be the state you receive your computer.
When it blinks green, it passed the boot check, and the boot firmware can be trusted. Then it checks that all /boot files are unmodified before it automatically boots into the OS. This should be the state you receive your computer.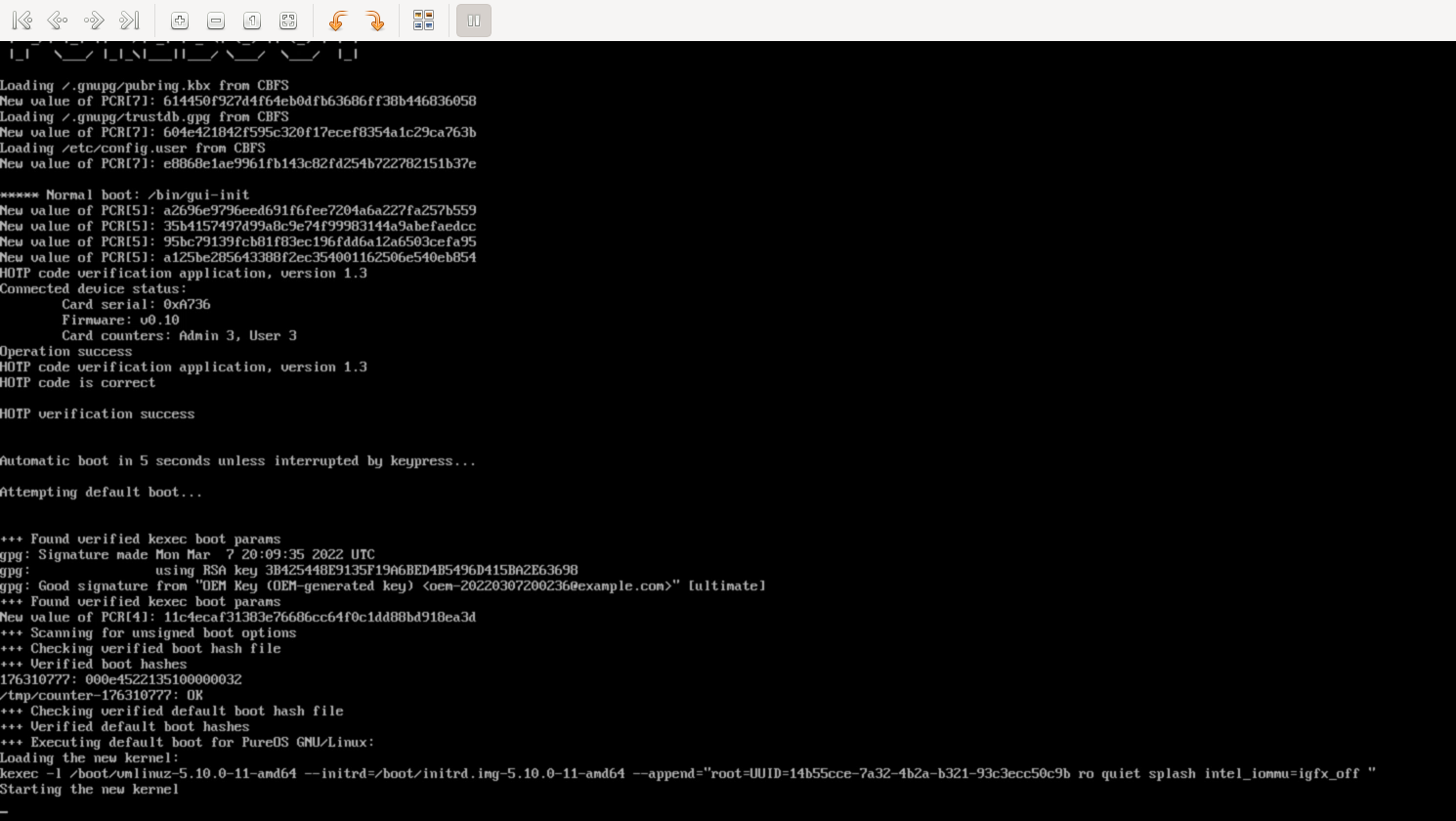 First Update
First Update
Once you’re fully booted and your accounts have been set up, installing updates regularly is essential for maintaining good security. Open the store, refresh your repositories and install the updates.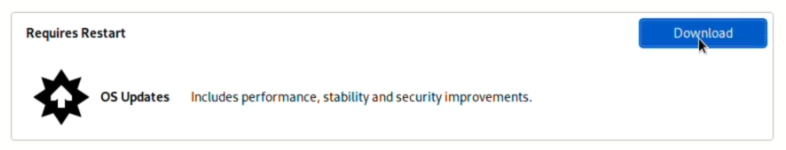 During this process, you’ll be asked to reboot to apply the updates; after the updates install, your computer will reboot once more, and you’ll have the option to update your boot files. This is normal when installing updates; select yes to update your checksums.
During this process, you’ll be asked to reboot to apply the updates; after the updates install, your computer will reboot once more, and you’ll have the option to update your boot files. This is normal when installing updates; select yes to update your checksums. 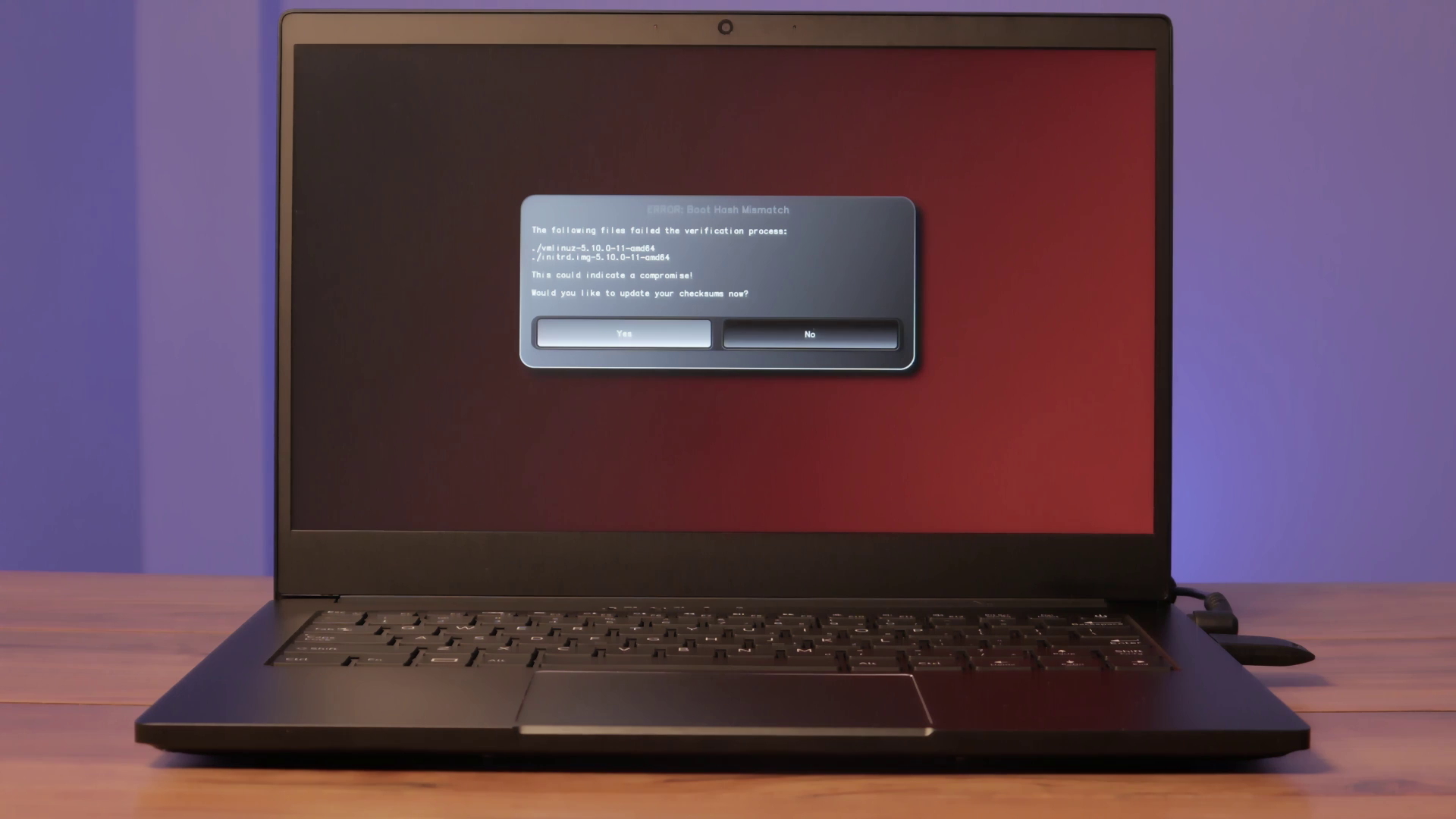 Next, with your Librem Key attached, press enter, then type your PIN; by default, this is 123456.
Next, with your Librem Key attached, press enter, then type your PIN; by default, this is 123456.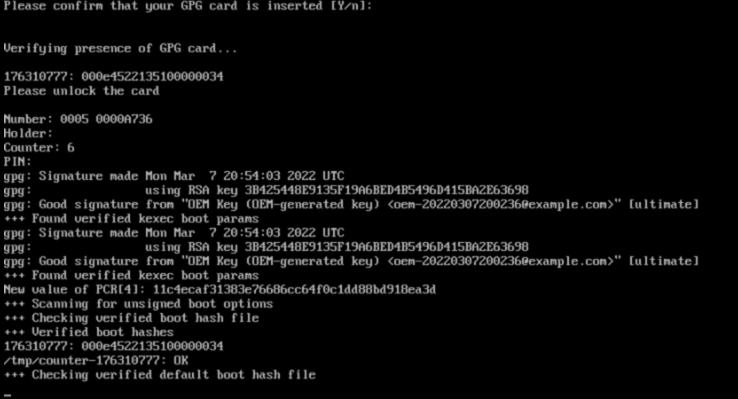 This will mark your updates as valid changes to your boot files.
This will mark your updates as valid changes to your boot files.
If you’re preparing to be away or in an untrusted environment, installing updates before your trip is a good method to prevent false positives from updates.
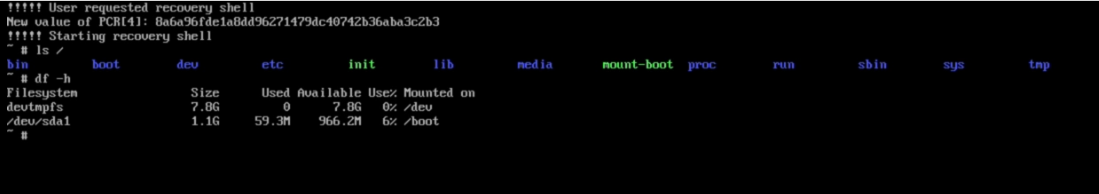
Detecting Tampering
If you startup your Librem device and tampering is detected, you’ll be able to abort the boot and investigate. 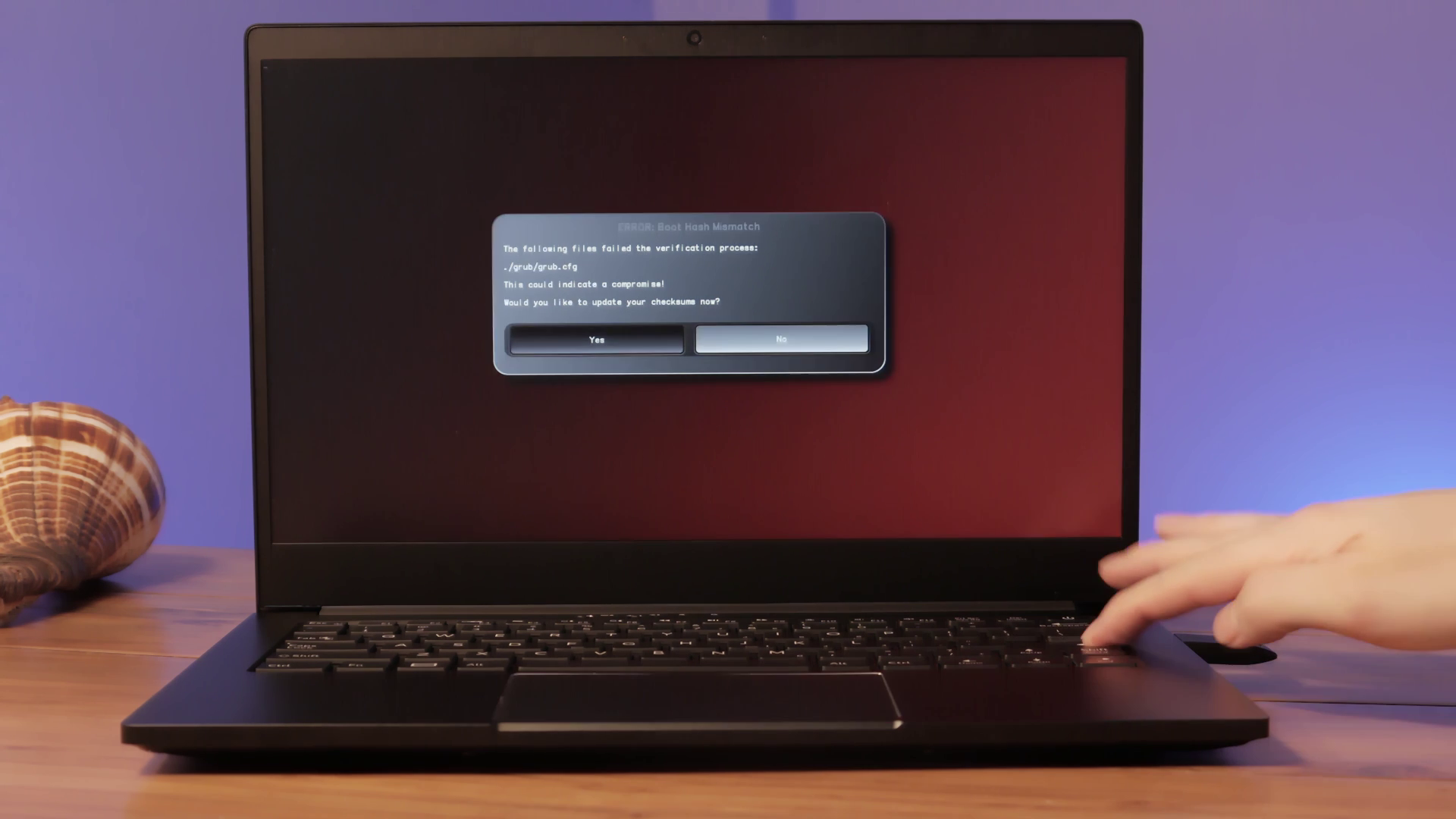 For example, you can examine the affected files from within PureBoot itself or a live USB OS. If you suspect the OS has been tampered with you can then completely replace it before it can run possibly malicious code. Whether you need the complete protection of PureBoot or just need peace of mind, PureBoot knows when to get in the way and when to quickly and quietly verify and boot your computer.
For example, you can examine the affected files from within PureBoot itself or a live USB OS. If you suspect the OS has been tampered with you can then completely replace it before it can run possibly malicious code. Whether you need the complete protection of PureBoot or just need peace of mind, PureBoot knows when to get in the way and when to quickly and quietly verify and boot your computer.
Protect your firmware and software on the hardware you own with PureBoot.
Purism Products and Availability Chart
| Model | Status | Lead Time | ||
|---|---|---|---|---|
 | Librem Key (Made in USA) | In Stock ($59+) | 10 business days | |
 | Liberty Phone (Made in USA Electronics) | Available on backorder ($1,999+) 4GB/128GB | n/a | |
 | Librem 5 | In Stock ($799+) 3GB/32GB | 10 business days | |
 | Librem 11 | Out of stock | New Version in Development | |
 | Librem 14 | Out of stock | New Version in Development | |
 | Librem Mini | Out of stock | New Version in Development | |
 | Librem Server | In Stock ($2,999+) | 45 business days | |
 | Librem PQC Encryptor | Available Now, contact sales@puri.sm | 90 business days | |
 | Librem PQC Comms Server | Available Now, contact sales@puri.sm | 90 business days |
Recent Posts
Related Content
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence
- PureOS Crimson Development Report: March 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale
- PureOS Crimson Development Report: January and February 2026 – Beta Released
- Privacy Under Siege


