Android’s Secret Backdoor, and How Purism’s Business Model Avoids This Type of Threat
Todd Weaver
PGP Fingerprint: B8CA ACEA D949 30F1 23C4 642C 23CF 2E3D 2545 14F7
Latest posts by Todd Weaver (see all)
- Closing the App Gap; Focus and Momentum - September 9, 2025
- Hardware Encrypted COMSEC Bundle by Purism - April 29, 2024
- Purism Differentiator Series, Part 14: Surveillance Capitalism - April 23, 2024

Today we learned once more why utilizing pure free software where the source code is available is critical to protect users’ rights to privacy, security, freedom, and anonymity.
The New York Times points out that this latest security breach “shows how companies throughout the technology supply chain can compromise privacy, with or without the knowledge of manufacturers or customers.”
Let’s examine the problem and see what can be done about it. It’s not too late to stand up for your rights.
The Fundamental Problem
All phones and tablets on the market today suffer from the same problem: the code that operates those devices are a mystery to the users. In this specific case Google’s Android, but the same problem exists with Apple devices and Windows devices, where the operating system, software-updated firmware, and most software that runs on those devices do not have the source code available to verify that there are no backdoors sending your private data to unwanted third parties.
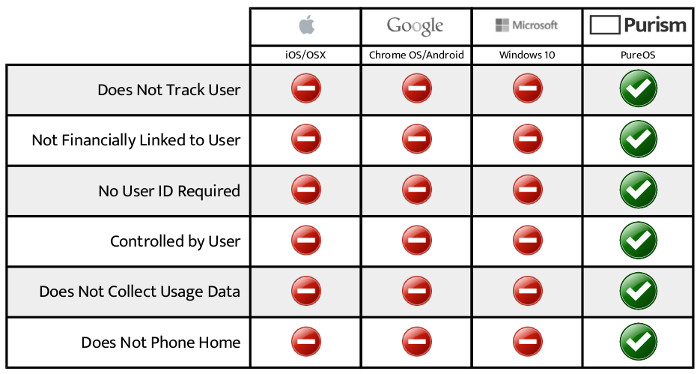
What this means is there is absolutely no way, for a user of Android, iOS, OSX, Windows, or any operating system that does not release all the source code, to guarantee he/she is not being illegally spied upon for nefarious reasons, corporate surveillance, government spying, and/or private data mining.
The tracking built into mobile devices is at every level imaginable. We need to create a better, digital rights respecting future for computing.
The Future of Computing
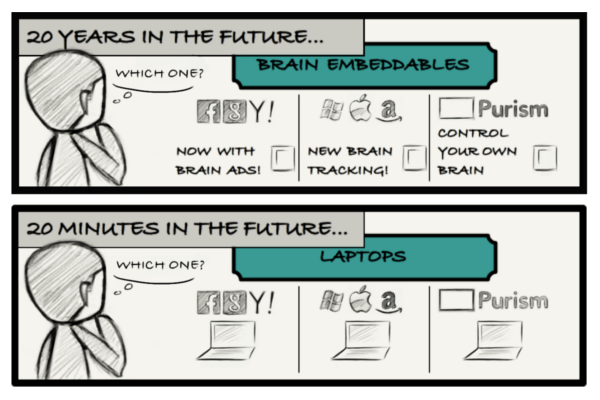 If we, as users, continue to morally and financially support Android, iOS, OSX, Windows or any other operating system that strip away the digital rights of users, we continue to advance a future where:
If we, as users, continue to morally and financially support Android, iOS, OSX, Windows or any other operating system that strip away the digital rights of users, we continue to advance a future where:
- users are controlled for profit;
- private data is mined for advertising revenue;
- governments spy on people;
- corporations capitalize on every user interaction;
- security breaches involve staggering amounts of personal data, with enormous consequences for individuals—even worse than what we’ve been seeing in recent years.
Every time you purchase a device from hardware companies that pre-install Android, iOS, OSX, Windows, and other nonfree operating systems, you are contributing to the erosion of your rights. Buying an HTC device benefits HTC, Google, the carrier, and all software companies that preinstall their privacy-stripping binaries. Similarly, buying Apple benefits Apple, the carrier, and all software apps preinstalled or even later installed.
The Solution
- Use a free software operating system, where the source code is released.
- Use hardware that allows you to run a completely freed operating system, where there is no mystery binaries, no private data delivered anywhere, and most importantly that you control.
- Support companies and organizations like Purism, and know that every penny of a purchase goes to benefit the future of computing and the digital rights for users. Make informed purchasing decisions and support hardware manufacturers that push Free Software’s agenda all the way through the supply chain.
The Upcoming Purism Phone and services infrastructure
Subscribe to our newsletter (simply send an email to announce-join@announce.wp.puri.sm to subscribe automatically) or follow us (see website footer for social links), then you will be notified when Purism launches the first freedom, security, and privacy respecting phone.
Recent Posts
Related Content
- Landfall: A Case Study in Commercial Spyware
- Librem PQC Encryptor: Future‑Proofing Against Both SS7 and Quantum
- Code is Power!
- Dialing Back to Move Forward: Why the Landline Revival Signals a Future for Privacy
- Purism Approach vs. Google Model


