Introducing PureBoot Basic
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
PureBoot is our high-security, tamper-detecting boot firmware that we offer as an alternative to our default coreboot firmware on hardware like our Librem 14 and Librem Mini. The combination of PureBoot, our anti-interdiction services, and the option of Qubes as the pre-installed OS makes hardware like the Librem 14 among the most secure computers you can buy. We are constantly adding improvements to PureBoot, and the release of PureBoot version 22 has added a new feature we are calling “PureBoot Basic” that lets you optionally disable the tamper detection. In this blog post I will discuss why we created this feature, where it’s useful, and some of our future plans for it.
A Quick PureBoot Primer
It is easier to understand what PureBoot Basic does once you understand how PureBoot normally works. Normally PureBoot pairs with a Librem Key and shares a secret between that Librem Key and the TPM on the computer. When the computer boots, it sends measurements of all of the initial code that runs to the TPM. If those measurements match a “known good” state set previously, the TPM will release a shared secret that gets converted into a 6-digit code. This code is similar to the codes you might use for two-factor authentication on websites, only instead of you authenticating to a server, the computer is authenticating to the Librem Key. The Librem Key uses its copy of the shared secret to create its own 6-digit code. If the codes match, the Librem Key blinks green, indicating the computer’s boot firmware hasn’t been tampered with. Otherwise it blinks a steady red.
After the boot firmware is trusted, PureBoot scans the files in /boot which contains your operating system’s kernel and other important files for booting into the OS. It validates these files with signatures based on private GPG keys stored on your Librem Key. If any of them have been tampered with, it will warn you of the changes so you can either sign them (in the case you changed the files yourself) or investigate further. Otherwise if everything matches, it will automatically boot into the system.
The Librem Key is a critical piece of what makes PureBoot work, because you can unplug the Librem Key and keep it with you, allowing you to detect any tampering that might be done while your computer is unattended. Yet this also means to use PureBoot instead of our default coreboot firmware, you must also have a Librem Key. At least until now.
PureBoot Basic
PureBoot Basic mode allows you to disable all of the tamper detecting features within PureBoot, leaving you with a simple but powerful boot environment that doesn’t require you to have a Librem Key. Why would you want to disable tamper detection? While tamper detection is the primary feature that makes PureBoot useful, it’s not the only one. PureBoot also offers a powerful recovery console that gives you many more troubleshooting and recovery tools for a system that won’t boot compared to coreboot and Grub, due to the fact that it’s a complete (if tiny) Linux environment all on its own.
While we have gone to great lengths to make PureBoot easy to use, it is still more complicated than our default coreboot install. Most of that complexity comes from tamper detection and the fact that routine system updates and other changes will trigger warnings the next time you boot, prompting you to re-sign files using your Librem Key. This extra complexity isn’t for everyone, which is one reason we still offer regular coreboot and don’t ship PureBoot on systems by default (the other reason is that it would require our customers to buy a Librem Key with every hardware purchase). Yet with tamper detection removed, PureBoot Basic provides many more features than our default coreboot firmware while still being very easy to use.
Another reason for PureBoot Basic mode is to make it easier for more people to try out PureBoot. Currently if you order a laptop with PureBoot, try it out, and decide the extra complexity is not for you, you have to go through additional steps to download and flash our default coreboot firmware over the top of it. This is also true if you are currently using coreboot but want to try out PureBoot. With PureBoot Basic mode, you can easily downgrade from full PureBoot protection, or enable it, all without replacing your boot firmware.
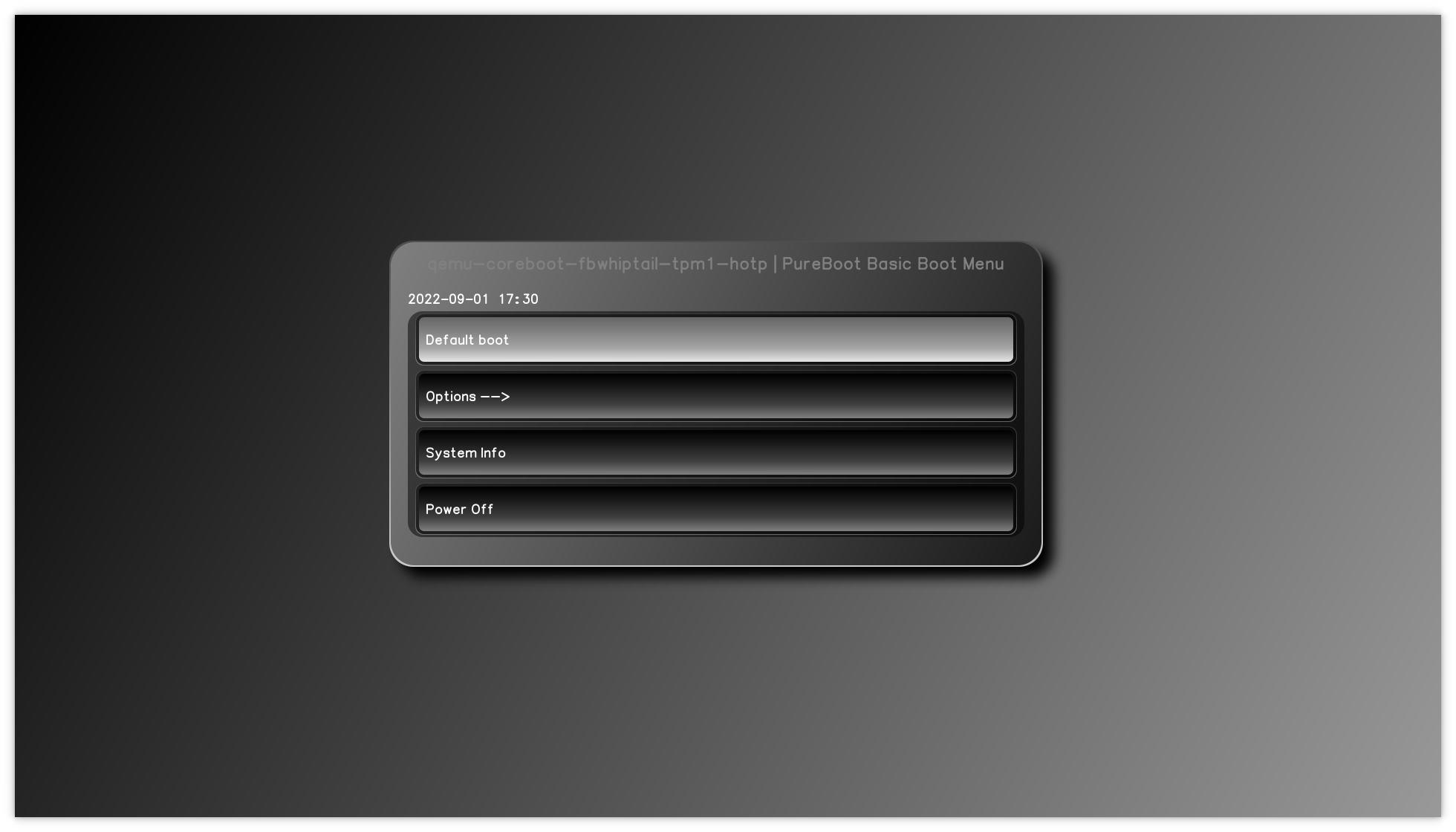
To try out PureBoot Basic, upgrade your existing PureBoot firmware to version 22 or greater. Then to enable PureBoot Basic mode, select Options -> Change Configuration Settings -> Enable PureBoot Basic Mode.
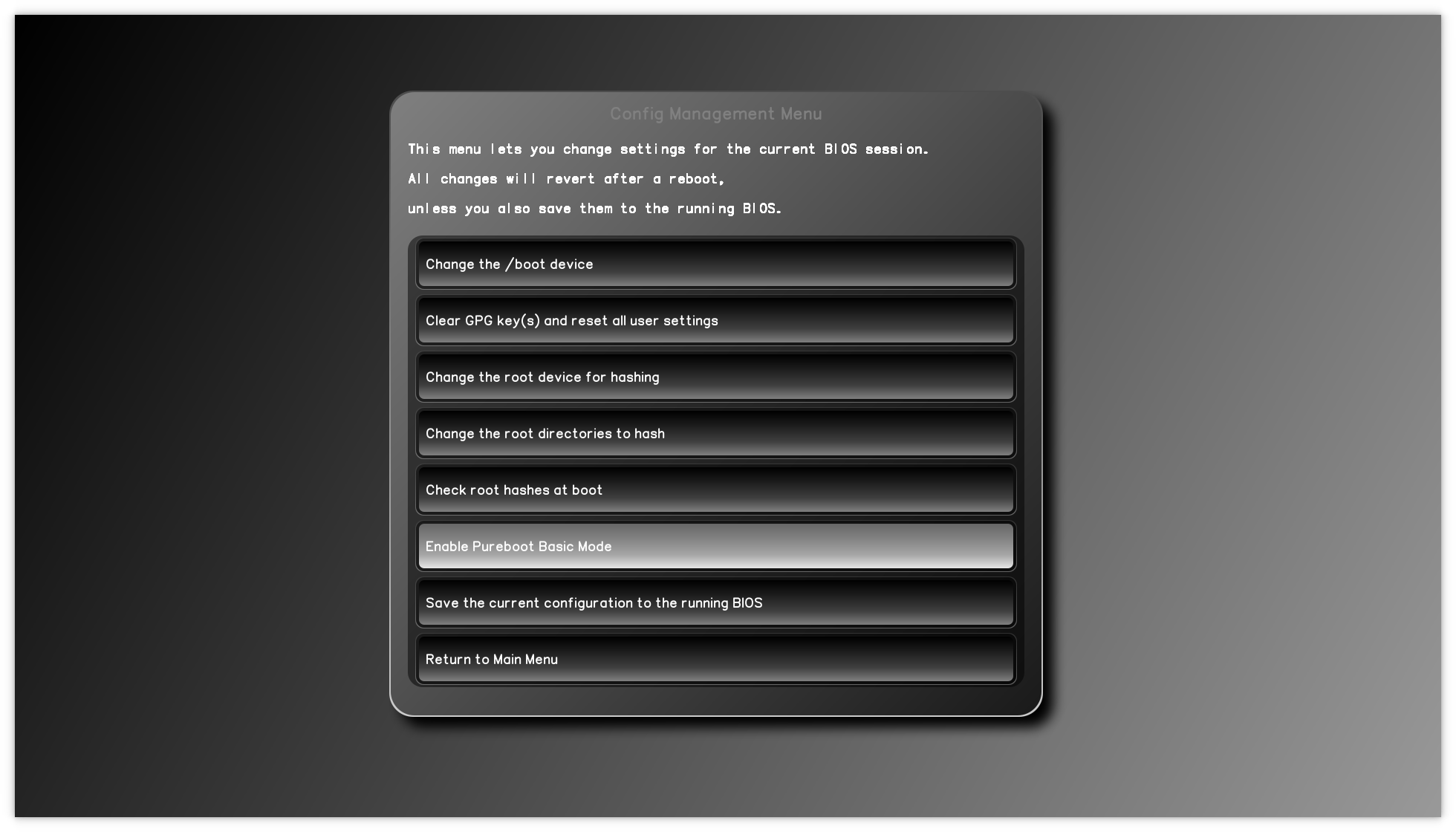
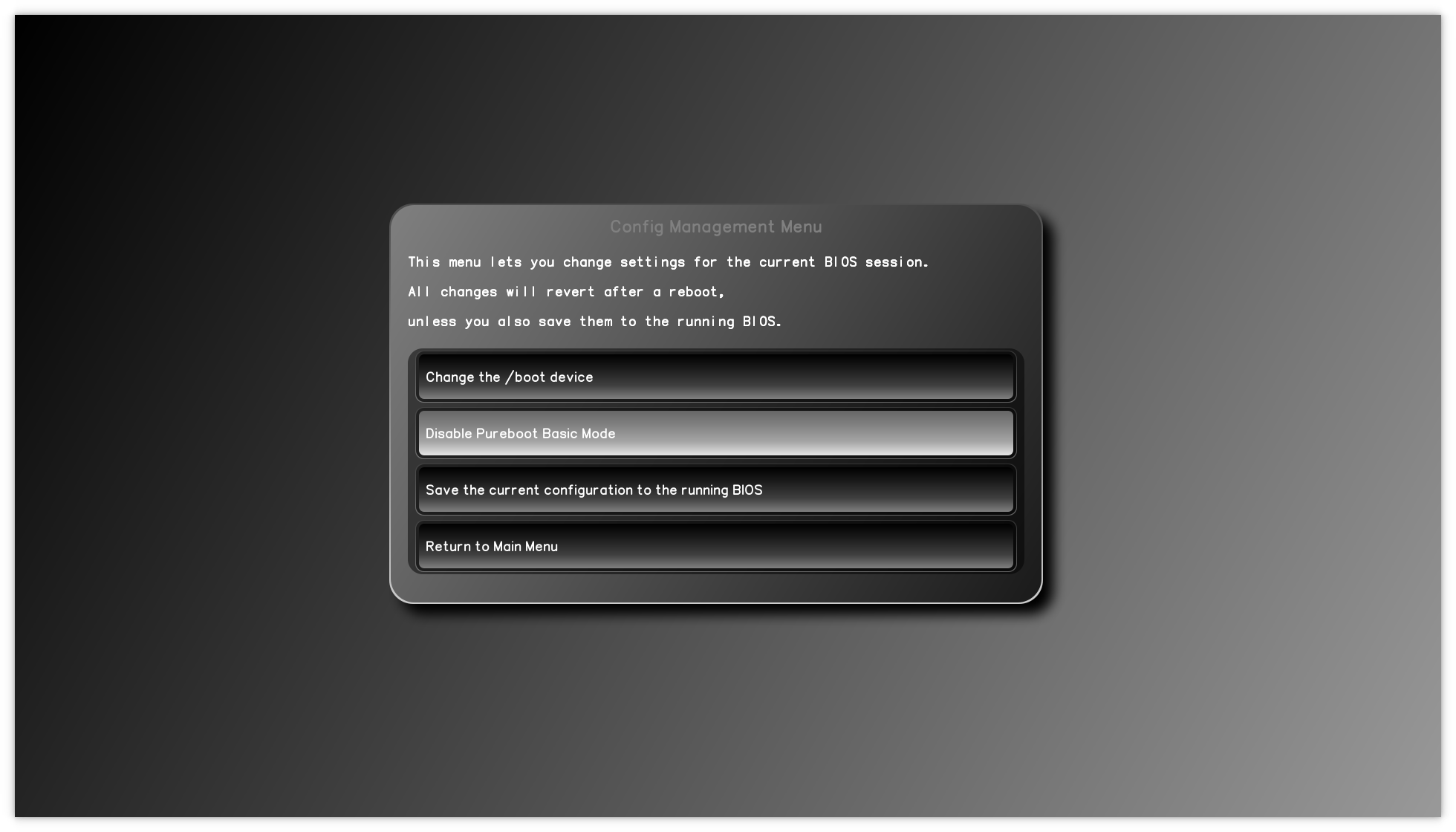
Once enabled, the PureBoot menu becomes much simpler as all of the options relating to tamper detection are removed. If you want to go back to regular PureBoot, you can disable Basic Mode it by selecting Options -> Change Configuration Settings -> Disable PureBoot Basic Mode.
The Future of PureBoot Basic
Now that we have released PureBoot Basic, we want to allow time for all of you to test it and give feedback. We hope to offer it as an option in our store soon and we are also considering making it the default choice instead of coreboot for future hardware at some point. If we do decide to go that route, we will still offer coreboot as a pre-installed option, and still maintain it for our hardware so you can always switch to it if you prefer.
We are really proud of the progress we have made with PureBoot over the years, and think having boot firmware that can protect your security with keys you control is incredibly important. PureBoot Basic will make it easier for more people to get some the advantages of PureBoot even if they don’t have a Librem Key or aren’t ready to turn on tamper detection. With PureBoot, you are in control of your own security.
Purism Products and Availability Chart
| Model | Status | Lead Time | ||
|---|---|---|---|---|
 | Librem Key (Made in USA) | In Stock ($59+) | 10 business days | |
 | Liberty Phone (Made in USA Electronics) | Available on backorder ($1,999+) 4GB/128GB | n/a | |
 | Librem 5 | In Stock ($799+) 3GB/32GB | 10 business days | |
 | Librem 11 | Out of stock | New Version in Development | |
 | Librem 14 | Out of stock | New Version in Development | |
 | Librem Mini | Out of stock | New Version in Development | |
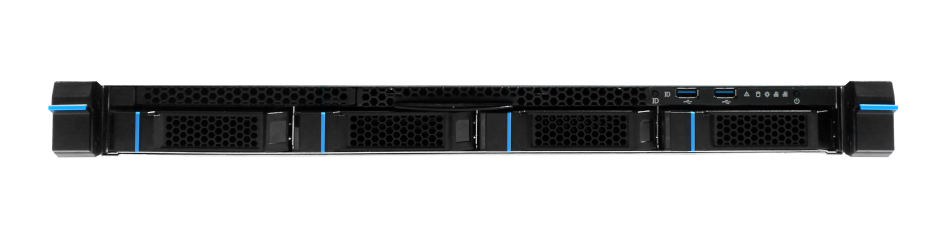
 | Librem Server | In Stock ($2,999+) | 45 business days | |
 | Librem PQC Encryptor | Available Now, contact sales@puri.sm | 90 business days | |
 | Librem PQC Comms Server | Available Now, contact sales@puri.sm | 90 business days |
Recent Posts
Related Content
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence
- PureOS Crimson Development Report: March 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale
- PureOS Crimson Development Report: January and February 2026 – Beta Released
- Privacy Under Siege


