Librem adds tamper-evident features, now most secure laptop under full customer control
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
Protecting customer privacy, security and freedom is so fundamental to Purism’s mission that we codified it in our Social Purpose Corporation charter. We believe that these three concepts of privacy, security, and freedom are not just important by themselves but are also dependent on each other. For example, it’s obvious that by improving your security, we help protect your privacy. What might be less obvious is how dependent your privacy is on your freedom. True privacy means your computer and data are under your control, not controlled by unethical big-tech corporations. When your digital life is under your control you have the freedom to share your data only when you want to. So as we consider ways to improve your security, it can’t be at the cost of privacy or freedom.
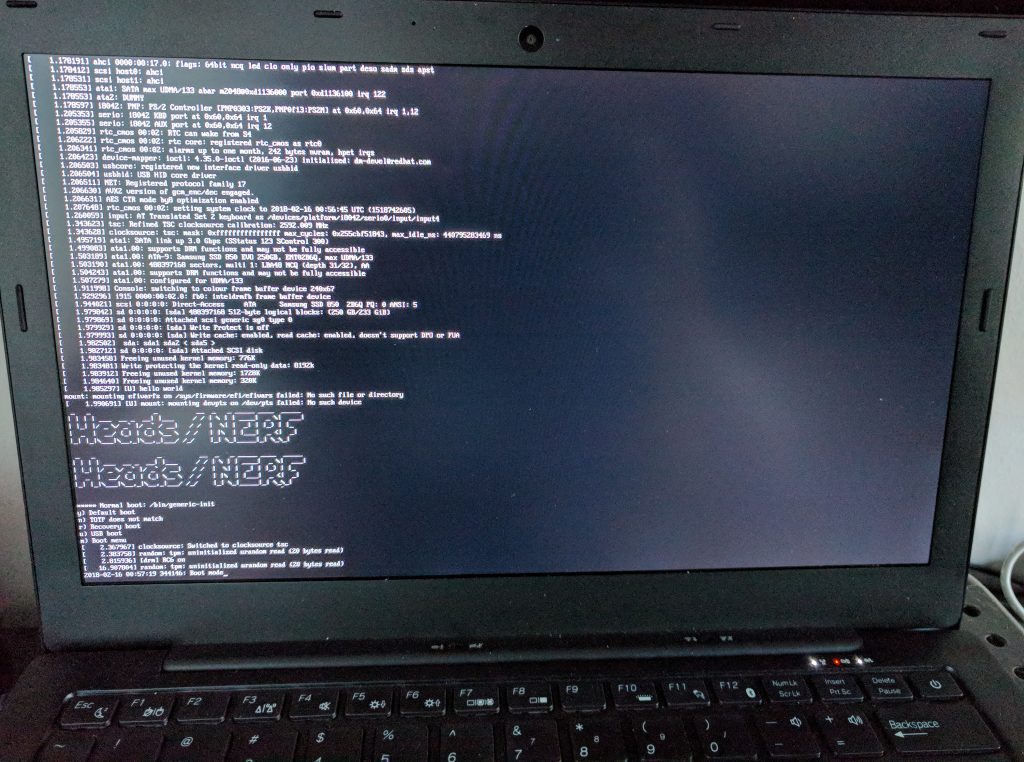
As part of our goal to improve security we are excited to announce that we have successfully integrated Heads into our TPM-enabled coreboot-running Librem laptops. This integration effort began in April 2017 with the partnership of Purism and Trammell Hudson’s Heads project, which required hardware design changes, coreboot modifications, and operating system updates to reach where we are with this announcement today. We now have a tamper-evident boot process starting with the BIOS all the way through verifying that the kernel, initrd, and boot configuration files haven’t been changed in any way. Soon Heads will be enabled by default on all our laptops and this critical piece combined with the rest of our security features will make Librem laptops the most secure laptop you can buy where you hold the keys.
In this post we will describe why Heads is such an integral part of our security and how it combines with the rest of our features to create a unique combination of security, privacy and freedom that don’t exist in any other laptop you can buy today.
Why Tamper-Evident Software Matters
For your computer to be secure, you need to be able to trust that your software hasn’t been modified to run malicious code instead. This is one of many reasons why it’s so important that you can see the source code for all of the software on your system from your web browser to your hardware drivers to the kernel and up to your BIOS. We’ve gone to great lengths to choose hardware that can run with free software drivers, load our laptops with the FSF-endorsed PureOS, use coreboot as our Free/Libre and Open Source BIOS, and have neutralized and disabled the Intel Management Engine.
Unfortunately being able to see the source code isn’t enough. All of the software you run trusts the kernel, and the kernel trusts the BIOS. Without tamper-evident features that start the moment the computer turns on, an attacker can inject malicious code into your BIOS or kernel with no way to detect it. Once started, that malicious software could capture your encrypted disk or login passwords along with any other secrets or other personal information on your computer. By running tamper-evident software at boot, you get peace of mind that your system can be trusted before you start using it. With Purism’s combined approach the first bit loaded into the CPU is measured and signed by the user to prove nothing has been tampered with.
Heads Above the Rest
There are a number of different technologies we could have chosen to protect the boot process, but unfortunately very few of them are Free/Libre and Open Source and almost all of them work by taking control away from you and putting it into a vendor that owns the keys that determine what software you can run at boot. We have witnessed first-hand unethical laptops that ship with “Secure Boot” enabled (a technology that only allows software signed with pre-approved (e.g. paid-for) corporate controlled keys to run at boot). The very limited BIOS on this machine offered no way to disable Secure Boot so it is impossible to install Debian, PureOS or any other distribution that hadn’t gotten the BIOS vendor and Microsoft’s (paid) approval.
Heads has a lot of advantages over all of the other boot verification technologies that make it perfect for Librem laptops. First, it is Free Software that works with the Open Source coreboot BIOS so you don’t have to take our word for it that it is backdoor-free–anybody is free to inspect the code and build and install it (and customize it) themselves.
Second, the way it uses the TPM on your system to provide tamper-evidence puts the keys under your control, not ours. The fact that you retain control over the keys that secure your system is incredibly important. While we intend to make the secure boot process painless, we also don’t think you should have to trust us for it to work–you can change your keys any time.
Enterprise Level Security, Easily
If you manage a fleet of machines, this means with Purism Librem laptops that include TPM and Heads, you now have the ideal platform that you can tailor for your specific enterprise needs with custom features and your own trusted company keys. You can provide a trusted boot environment that protects your users from persistent malware and detects tampering while they travel, while still integrating with your custom in-house laptop images. And you can do this without having to ask us to sign your software.
The IT Security department’s dream of self-signed, tamper-evident, persistent-malware-detecting, laptop computer is now a reality with Purism Librem laptops.
Part of a Bigger Story
Having a secure boot process is the foundation of security on a modern laptop but it’s only part of the reason why Librem laptops are so secure. Here we will review some of the other security features that when combined with Heads puts Librem laptops in a totally different league.
Snitches get Switches
One of the first security features that set us apart was our hardware kill switches. Unlike a software switch that asks the hardware to turn off politely and hopes it listens, our hardware kill switches sever the circuit at the hardware level. This means you don’t have to worry about Remote Access Trojan malware that can disable your webcam LED to spy on you more easily. When you hit the radio kill switch, your WiFi is completely off, and when you hit the webcam/mic kill switch, the webcam is truly powered off–no webcam stickers needed.
Extra Security with Qubes
Our laptops default to PureOS because we feel it provides the best overall desktop experience for every type of user while still protecting your privacy, security and freedom. For customers who want an even higher level of security, Qubes uses virtualization features to provide extra security through compartmentalization. In 2015, our Librem 13 (version 1) was the first (and currently only) hardware to have received Qubes certification. Our current line of laptops remains compatible, and we recently announced that our current generation of Librem 13 and 15 laptops now fully work with Qubes 4.0.
We are also investigating ways to incorporate some of the compartmentalization features of Qubes into PureOS so you can still have good security but with an easier learning curve. Disposable web browsers and protected USB ports are just some of the features we are considering.
We Won’t Stop There
When you combine tamper-evident secure booting with Heads, an Open Source coreboot BIOS, a neutered and disabled Intel Management Engine, hardware kill switches, and the advanced security features of Qubes, Librem laptops have a security advantage over any other laptop you can buy. Equally important, they have extra security without sacrificing your privacy, freedom, or control. While we are excited to hit this major milestone, and can’t wait to have Heads on by default for all our laptops, we aren’t stopping there.
A secured boot process opens the possibility for even stronger tamper-evidence that extends further into the file system. From there you can move past tamper-evidence into tamper-resistance or even tamper-proofing in some advanced applications. We are also investigating better ways to incorporate hardware tokens with our products to provide more convenient authentication and encryption while still leaving the keys in your hands.
Ultimately, our goal is to provide you with the most secure computer you can buy that protects your privacy while also respecting your freedom. Since these values are inter-dependent, each milestone that improves one ultimately strengthens them all, and we will continue to work to raise the bar on all of them.
Recent Posts
Related Content
- Purism Liberty Phone Exists vs. Delayed T1 Phone
- Code is Power!
- Introducing the Librem PQC Comms Server
- Introducing the Librem PQC Encryptor
- Abside and Purism Partner to Deliver Secure Mobile Solution for U.S. Government and NATO Countries


