Tamper-evident Boot Update: Making Heads More Usable
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
We announced not too long ago that we have successfully integrated the tamper-evident boot software Heads into our Librem laptops. Heads secures the boot process so that you can trust that the BIOS and the rest of the boot process hasn’t been tampered with, but with keys that are fully under your control.
Heads is cutting edge software and provides a level of security beyond what you would find in a regular computer. Up to this point though, its main user base are expert-level users who are willing to hardware flash their BIOS. The current user interface is also geared more toward those expert users with command-line scripts that make the assumption that you know a fair amount about how Heads works under the hood.
We want all our customers to benefit from the extra security in Heads so we intend to include it by default in all of our laptops in the future. For that to work though, Heads needs to be accessible for people of all experience levels. Most users don’t want to drop to a recovery shell with an odd error message so they can type some commands if they happen to update their BIOS, and they don’t want to be locked out of their system if they forgot to update their file signatures in /boot after a kernel update.
When we announced that we were partnering with Trammell Hudson to use Heads on our laptops, we didn’t just mean “thanks for the Free Software, see you later!” Instead, we are putting our own internal engineering efforts to the task of not just porting Heads to our hardware, but also improving it–and sharing those improvements upstream.
The Delicious GUI Center
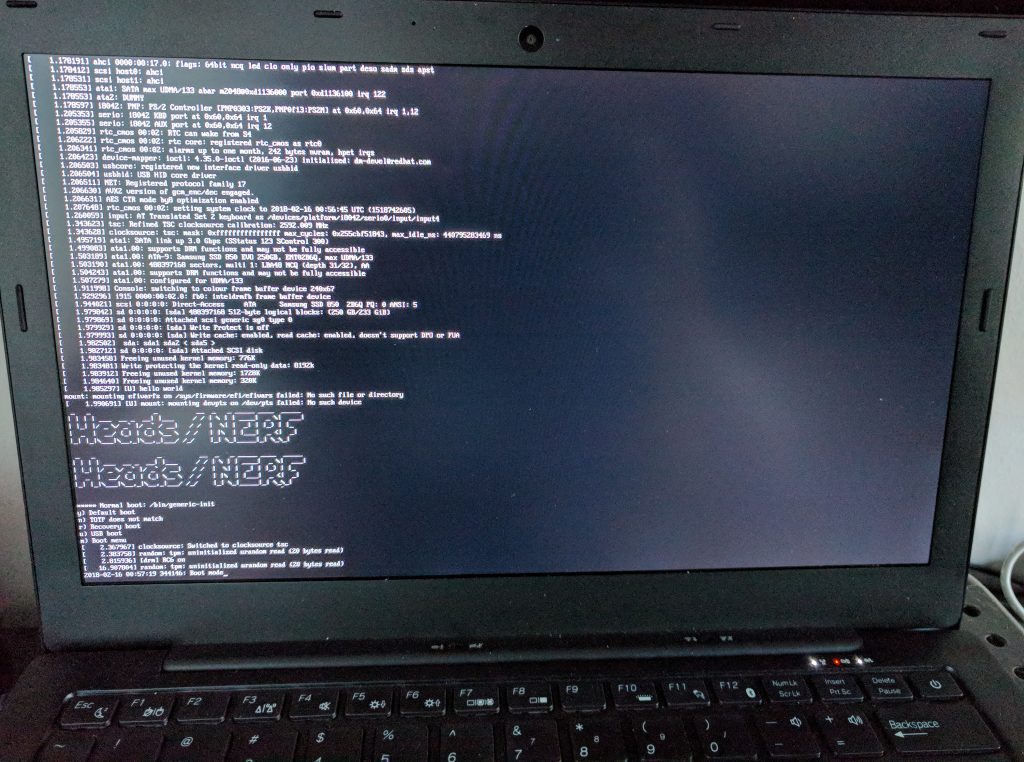
The first of our improvements is focused on making the boot screen more accessible. We started by added whiptail (software that lets you display GUI menus in a console) to Heads so that we can display a boot menu that more closely resembles GRUB. We then duplicated the features of the existing Heads boot menu so that instead of this:
you now see this:
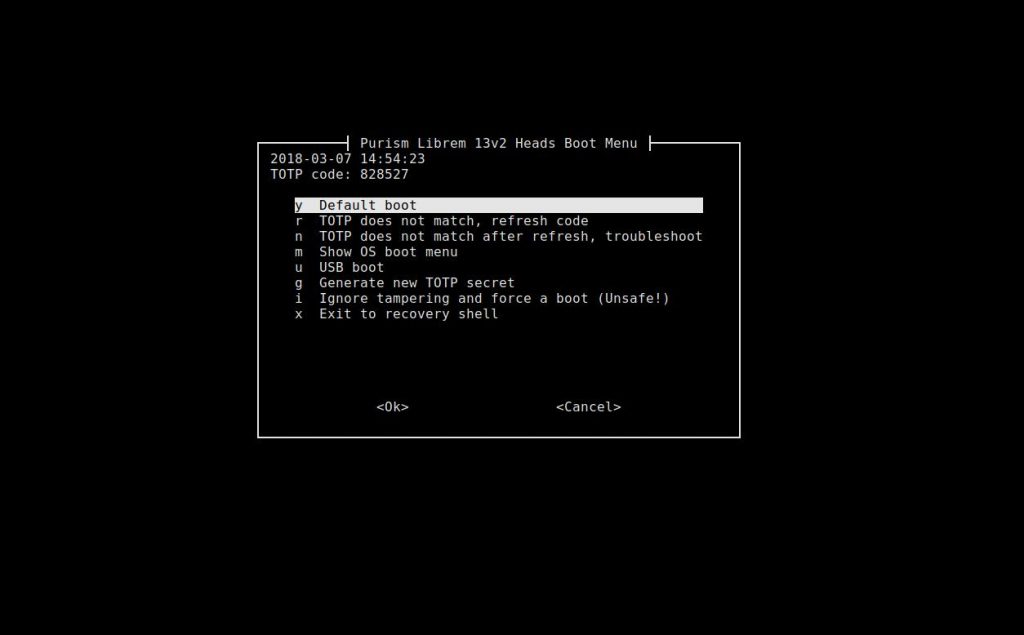
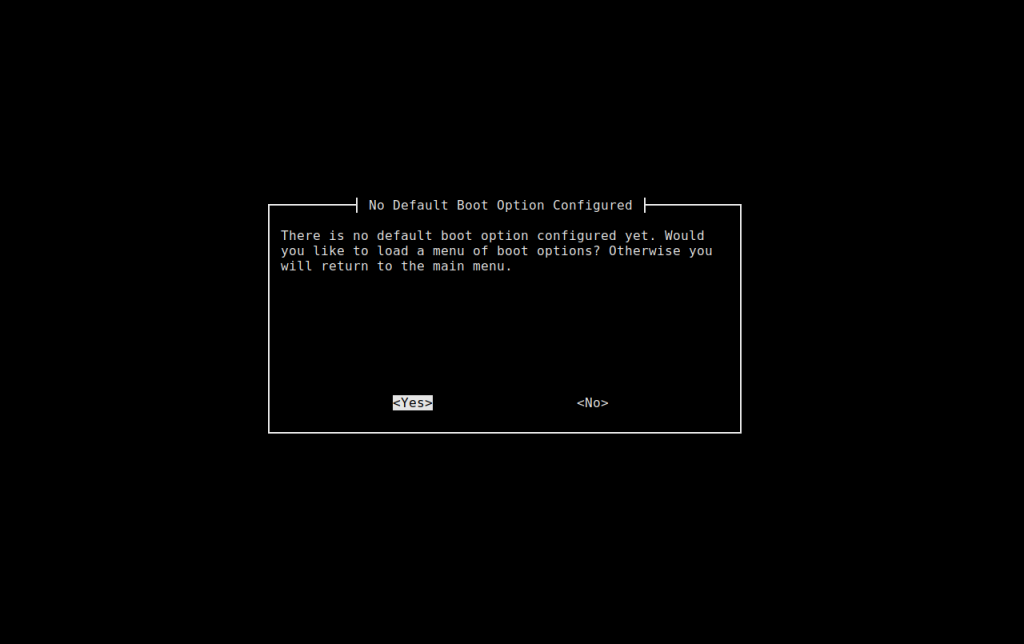
If you hit enter, you boot straight into your OS just like with GRUB, only behind the scenes Heads is checking all the files in /boot for tampering. If you hadn’t already configured a default boot option, instead of dumping you back to a main menu with no explanation or existing out to a shell, we decided to provide a GUI so you can decide what to do next:
If you decide to load a menu of boot options from the main menu or from this dialog, we also wrapped a GUI around the Heads boot menu that parses your GRUB config file:
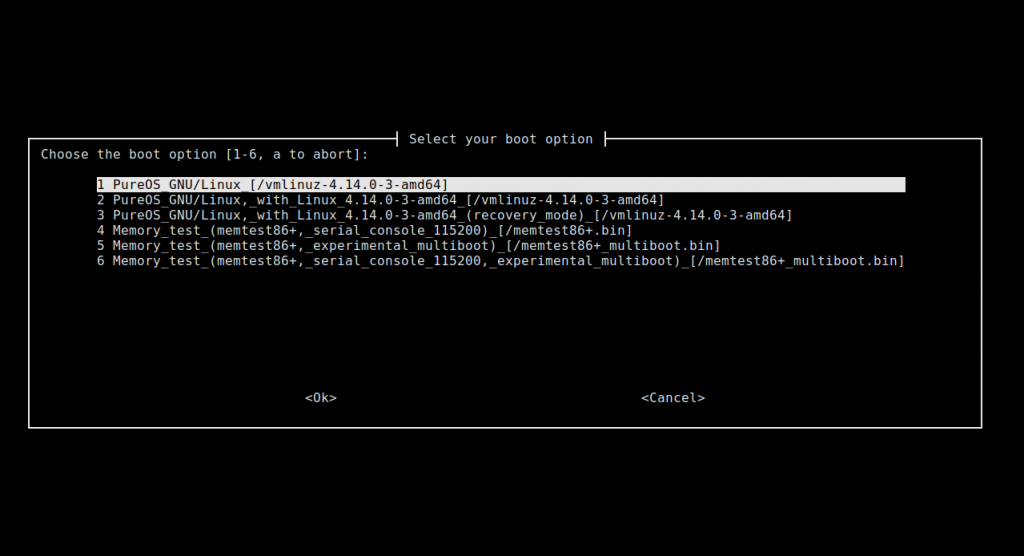
In each of the most common workflows, we’ve replaced the console output with an easier-to-use menu that also provides a bit more explanation on what’s happening if something goes wrong. For the most part the average user will just verify the TOTP code and then hit Enter to boot their system so in that way it’s not much different from a standard GRUB boot screen. These extra menus come in only if the user ever needs to deviate from the default and select a different kernel, generate a new TOTP code, or do other maintenance within Heads.
What’s Next
We now have these GUI menus working well in our internal Heads prototypes and we’ve also pushed our changes upstream, where most of them have already been pulled into the Heads project. That said, having a GUI boot menu is only part of what you need to make tamper-evident boot usable. Now that the boot menu is in a good place, our next focus is on making the overall Heads bootstrap and update process, key management, and signature generation easy (if only we had a GPG expert to help us with smart card integration, that would sure make things easier). Keep an eye out for more updates along all these lines soon.
Recent Posts
Related Content
- Code is Power!
- PureBoot Not Vulnerable to UEFI Exploits (Again)
- Intel AX200 Wi-Fi/Bluetooth Shipping for New Orders
- Librem 11 Memory Adventures
- PureBoot Framebuffer Boot Support


