Privacy in Depth
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026
In the security world there is a concept called “Defense in Depth” that refers to setting up layers of defense so that if an attacker bypasses one layer there are other layers they must contend with. In physical security this might take the form of a lock on the outside door of an office building, a security guard inside the foyer who identifies a visitor, access to different floors in the building protected by keycards in the elevator, additional locked rooms or safes on a particular floor for particularly sensitive property, and security guards patrolling the building and reviewing security camera footage. In the digital world this might take the form of firewalls, network segmentation, multi-factor authentication, event log monitoring, and malware scanners.
A similar approach, which I’ll call “Privacy in Depth” applies the same principles to privacy. When you have an attacker who is attempting to violate your privacy, you can assume that at some point they may be able to bypass one layer of defense, and if they do, you want to have additional layers available to protect your personal data. Protecting our customers’ privacy is a core tenet in our Social Purpose and in this post I will describe the layers of privacy defenses we have built into the Librem 14, Librem Mini, Librem 5 and Librem 5 USA product lines.
Privacy and Security
As I go into our different defenses, something that you might notice is that there is a lot of overlap between defenses that help protect your security and your privacy. Yet there is a distinct difference as well. Privacy defenses help protect you from attacks that attempt to access your personal data without your consent. Security defenses help protect you from attempts to steal or harm your property (including data).
It may seem that security defenses encompass both privacy and security, but there are subtle differences and areas where the two diverge. You don’t always need to resort to security measures to protect privacy. To take an example from the physical world, most clothing serves a privacy function but not a security function. A bullet-proof vest, a helmet, or work gloves are examples of clothing that primarily serve a security function but not a privacy function. To take an example from the digital world, one can protect privacy simply by not collecting data to begin with, but to secure data you would likely resort to encryption or forms of access control.
Control and Consent
Privacy is about control and consent. An individual must first have control over their data, before they can consent to share it with others. When Big Tech companies promise to protect your privacy, they mean from others, not themselves. They inherently trust themselves with your data and are convinced you should trust them too, regardless of their track record of privacy abuses.
The best example of this privacy double standard is the mass of personal data both iOS and Android users share with Apple and Google respectively on a daily basis. These companies might restrict competitors from your data, but that’s little comfort given their own unrestricted access. If you decide you no longer want to share your personal data with these companies, you will discover how little control you actually have.
Control and consent are important because privacy is not one-size-fits-all. Just like people have different sensibilities of how much of their body they wish to cover up with clothing, people also differ on what data about them is private and who they are willing to share it with. Our approach is to start with defaults that are on the stricter side of privacy protections, and grant as much control as possible to individuals so if they want to be stricter or more relaxed, it’s easy to switch.
Hardware
Privacy protections start with Purism hardware in the form of hardware kill switches. In my mind hardware kill switches remain the simplest and best way to demonstrate how Purism approaches both privacy and security differently. With hardware kill switches, you can control whether a particular piece of hardware is enabled, regardless of what an attacker might do to the OS. Instead of relying on software in the OS to disable the hardware, our switches actually disable the hardware itself so you know it’s off.
The webcam/microphone kill switch provides strong privacy protections against snooping and is much more convenient than a post-it note covering your webcam. Unlike a post-it note, it also extends to your microphone. Since most people only use that hardware during conference calls, you can leave it switched off most of the time, only enabling it briefly during those meetings.
Why is protecting your webcam and microphone so important for privacy? If you search for Remote Access Trojans (RATs) online you will find many articles about this seedy underbelly of the Internet where creeps hack people’s computers, access their webcams privately, record sensitive footage they barter with their community, and use it to extort their victims. There was even a feature film Ratter published in 2015 that dramatizes this sort of victimization. In some cases RATs are even able to disable the webcam LED on computers to make it harder to detect.
Librem 14
On the Librem 14, the hardware kill switches appear above the keyboard and allow you to disable the webcam and microphone with one switch, and the WiFi and Bluetooth with the other. By placing the kill switches front and center above the keyboard, it’s easy for you to confirm the current state with a glance.

The Librem 14 also includes a hardware Ethernet port, which can aid privacy by allowing you to connect to a network over a physical cable, instead of over an untrusted wireless connection that might be monitored.

Librem 5
On the Librem 5, we started with kill switches that disable the front and back cameras and microphone, and WiFi/BlueTooth, and added a third one that disables the cellular modem. Our entire phone design was actually built around the ability to disable (and even remove) the cellular modem in hardware both to make the phone more modular and repairable, as well as give you more control over your privacy.

Why is disabling the modem important for privacy? Most people are aware these days that if their cellphone is on and connected to a tower, that their location is constantly being logged–it’s required so cellular towers are able to forward incoming calls to you. This means wherever you go with a powered-on phone, your location is tracked. Yet most phones at best only offer two options if you want to disable this sort of tracking: use a software-based “airplane mode” in the OS, or power off the phone. In both cases, since the cellular modem often can run independently from the main CPU and OS, the only real way to ensure it’s truly off is to unplug the battery (if you can).
Compared to traditional computers, modern phones contain a range of other sensors like a GPS, compass, gyroscope, light sensors, and others that can be surprisingly revealing in the hands of clever data analysts. We wanted to give people a convenient way to control this hardware beyond traditional software switches, so we designed the Librem 5 with a feature we call Lockdown Mode.
To trigger Lockdown Mode, just flip all three kill switches. When you do, all the previous hardware along with all other sensors are disabled in hardware, not software. The Librem 5 in this state is still a standard, functional, offline computer, minus all the sensors. You can still read documents, play games, listen to music, or perform any other functions that don’t require a network or sensors. Plus you’ll get increased battery life as a bonus! When you are ready to go back online, just flip the switches back on.
Firmware
System firmware is the first code that a computer runs and generally speaking, attacks against firmware are aimed at compromising the computer’s security, and not necessarily its privacy. Yet even here we have made decisions that increase your privacy.
We offer both coreboot and PureBoot as boot firmware options on our Librem 14 as well as our Librem EC embedded controller firmware. These options use free software and generally we discuss them in the context of the freedom or security benefits they provide. The privacy benefits outside of the fact you can audit our code for spyware are a bit subtler.
The first decision we made is with respect to the Intel Management Engine (ME) we include in our boot firmware. While all modern Intel systems require some form of proprietary ME firmware, we start by choosing ME firmware without Active Management Technology (AMT) included. AMT allows enterprises to control systems in their fleet remotely including viewing what’s currently on the screen and taking full remote control over the network. We also trigger the disable bit in the ME so it isn’t active after initial power on.
Next, we ship with unlocked firmware that you can update and modify yourself, but that also allows you to boot the OS of your choice. We don’t require you to get signatures from us or other vendors to boot non-Purism OSes or load modified firmware and there is no need to jailbreak anything or disable security settings. If you choose to use our high security PureBoot firmware you will manage boot security with your own keys under your control, not ours, while still being able to boot the OS of your choice.
Why does this matter for privacy? Some vendors make it difficult to boot alternate OSes and require you to hack the firmware or disable security features and “jailbreak” it to do so. Yet often the base OS these systems ship with (particularly true of Android smartphones) are notorious for capturing your data. The only way to avoid those kinds of privacy invasions is by replacing the OS with one that removes those privacy-invading bits, at least if your vendor lets you.
Operating System
By default all our hardware, including our Librem 5 phones, ships with PureOS, which includes only free software. Why does this matter for privacy? One of the reasons privacy invasions are so rampant on smartphones and increasingly common on desktops, is that it’s easier to hide what an application is doing if you can’t inspect or modify its code.
Since you can inspect and change all of the software in PureOS, it’s much harder for a developer to sneak in code that attempts to harvest your data. If a developer did attempt such a thing, the community could easily ship an alternate version with those privacy invasions removed.
This ability to audit and change code in free software, along with a culture that values privacy, has resulted in free software largely being free from privacy invasions. The community simply wouldn’t stand for it.
For customers who want even more control at the expense of some convenience we also offer QubesOS as a pre-installed and supported option. While it is primarily aimed at security-minded customers, the fact that it lets you compartmentalize your data across different VMs and control how it’s accessed, also makes it a powerful way to protect your privacy.
Applications
While we have already established that free software is largely safe from the kinds of spyware and privacy invasions you see in the proprietary world, so you don’t have to second guess the intentions of weather, news, or contacts apps. Yet there are still additional places we can protect at the application level. One of the most important areas of focus here is the web browser in two main areas: websites tracking your behavior, and search engines tracking your search queries.
PureOS defaults to Gnome Web which includes a number of privacy-protecting defaults and uses DuckDuckGo instead of Google as its default search engine. We of course also offer FireFox for customers who prefer that browser. There is a reason Google spends billions of dollars to ensure it is the default search engine on many platforms. These days many people search for things not by visiting a search engine, but simply by typing search terms into the URL bar. Defaults matter, and by defaulting to a search engine that claims stronger privacy protections, there is one less privacy tweak you have to make.
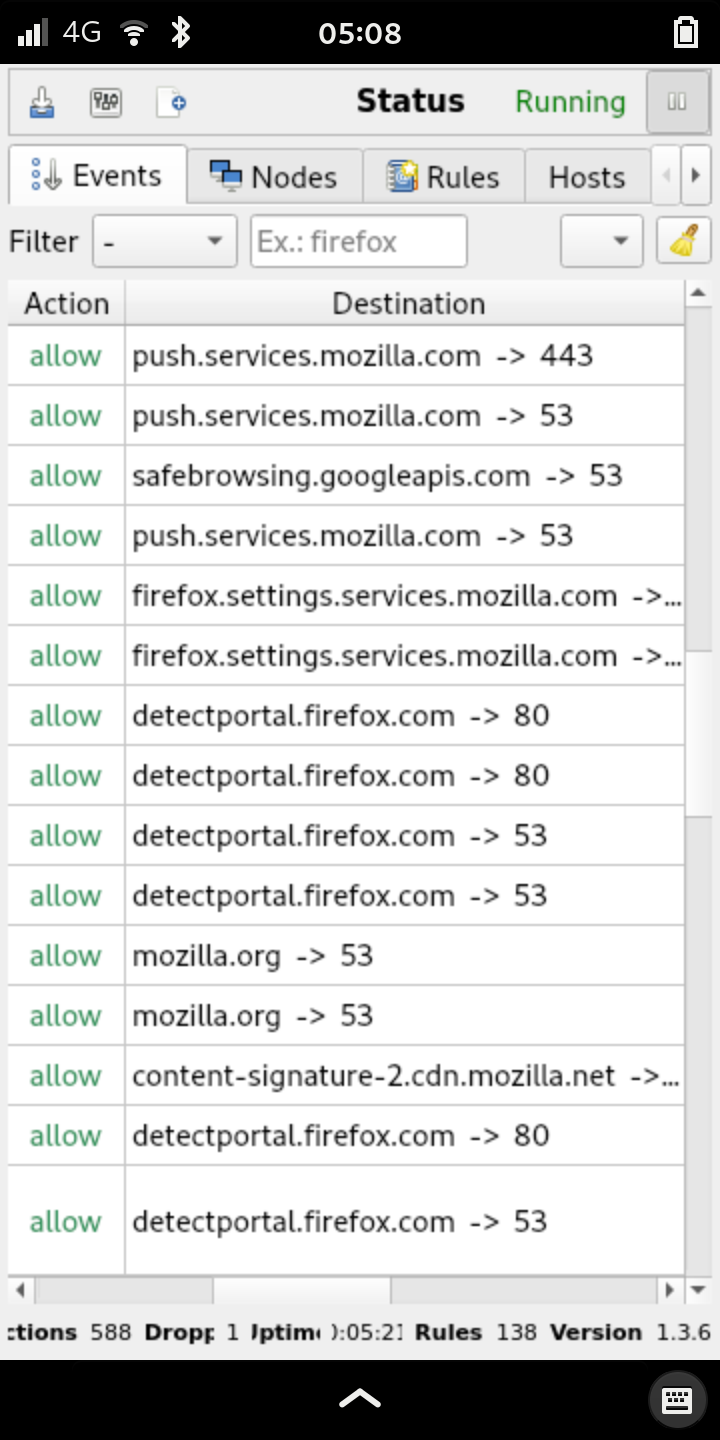
For customers who want additional privacy at the expense of some initial time spent training the app, you can also install the third-party OpenSnitch tool. I wrote about this tool in depth in this article, but essentially it acts as an application firewall that lets you monitor what connections applications make out to the Internet. With OpenSnitch you have even greater control over information that might leak from these apps and it works both on Librem 14 and the Mini, as well as the Librem 5.
Services
The final area we protect privacy is in the services we offer. Our Librem One suite of services combine our Librem Social social media platform, Librem Chat chat network, and for a monthly subscription, our Librem Mail email and Librem Tunnel VPN. All are designed to respect your privacy and offer alternatives to other service providers who directly profit from the data of their customers.
We also offer a suite of cellphone plans in the US designed specifically to protect customer privacy from providers intent on collecting and selling customer data. Our AweSIM service is an unlimited plan that works with either the Librem 5 or other unlocked phones in the US, and we also offer SIMple and SIMple Plus plans for people with more modest data needs. In all cases we act as a privacy proxy between our customers’ personal data and the cellular network they use so only we know the link between a phone number and the individual that uses it.
Corporate
Our ultimate defense is our Social Purpose charter, which defines the ethics that our company follows. Among other guiding principles is:
The Corporation will prioritize privacy, security, and freedom for its customers. The Corporation will place respecting users’ rights to privacy, security, and freedom at the forefront of its mission.
Because we are a Social Purpose Corporation, these values take a higher precedence than profit, unlike traditional C corporations that must prioritize maximizing shareholder value. By putting customer privacy in our charter, we have a guiding document we can point to whenever we have questions about how we should respond to a situation, and are protected against any potential future investor who might want us to “maximize shareholder value” by capturing and selling customer data. There are plenty of companies that will tell you how important your privacy is to them, but few that would be willing to embed protecting it into their corporate charter.
Conclusion
There are many ways that companies attempt to violate your privacy, so it makes sense for you to have many ways to defend it. Purism products provide privacy in depth with our hardware, firmware, software, applications and services, all following the guiding principles cemented in our corporate structure itself. The result is layers of defense that put you in control of your data, so you can consent to how it is used.
Purism Products and Availability Chart
| Model | Status | Lead Time | ||
|---|---|---|---|---|
 | Librem Key (Made in USA) | In Stock ($59+) | 10 business days | |
 | Liberty Phone (Made in USA Electronics) | Available on backorder ($1,999+) 4GB/128GB | n/a | |
 | Librem 5 | In Stock ($799+) 3GB/32GB | 10 business days | |
 | Librem 11 | Out of stock | New Version in Development | |
 | Librem 14 | Out of stock | New Version in Development | |
 | Librem Mini | Out of stock | New Version in Development | |
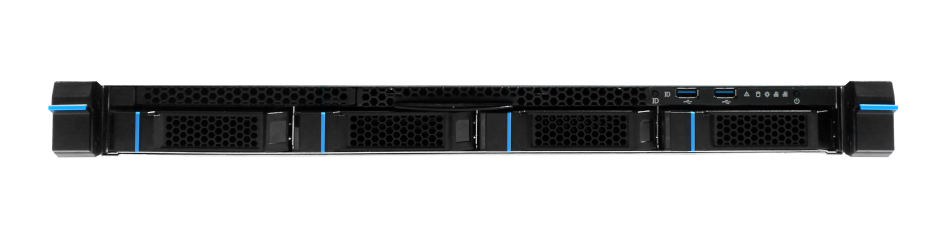
 | Librem Server | In Stock ($2,999+) | 45 business days | |
 | Librem PQC Encryptor | Available Now, contact sales@puri.sm | 90 business days | |
 | Librem PQC Comms Server | Available Now, contact sales@puri.sm | 90 business days |
Recent Posts
Related Content
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence
- PureOS Crimson Development Report: March 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale
- PureOS Crimson Development Report: January and February 2026 – Beta Released
- Privacy Under Siege


