Why The Librem 14 with QubesOS Exceeded My Expectations
Purism
Latest posts by Purism (see all)
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence - May 11, 2026
- PureOS Crimson Development Report: March 2026 - April 17, 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale - March 23, 2026

If you face extreme threats, or even if you are just looking for a high-security operating system for peace of mind, it’s hard to beat QubesOS. While it’s not as easy to use as our default PureOS, it offers a lot of advanced security features that, when combined with the advanced hardware and firmware security features of the Librem 14, makes for one of most secure computers out there.
I have been using QubesOS as my primary OS for many years now, starting with the 3.x release on both my work (Thinkpad X230) and personal (Librem 13v1) computers. Over the last couple years my primary work machine has been a Librem 13v4 running Qubes with 16Gb RAM and solid-state storage. Starting this summer I moved to a Librem 14 for my work computer, our dream laptop that we designed (at least in part) to run Qubes well by adding a fast, 6-core/12-thread CPU and expansion up to 64GB RAM. I’ve been using this laptop constantly over the past few months and I’m convinced that the Librem 14 is the best laptop for Qubes. In this post I wanted to offer a brief retrospective on my experience running Qubes as my primary OS on my Librem 14 compared to past computers.
Hardware Support
Hardware support has often been the trickiest part about switching to Qubes. Qubes relies heavily on Xen virtual machines for its security and every application runs inside different Xen VMs you create. If your hardware doesn’t support Xen extensions in the Linux kernel well, or doesn’t support hardware virtualization in Linux, Qubes might not install at all, or might only run at a degraded level of protection. Beyond that, some computers ship with graphics chips, WiFi or other hardware that requires specific, proprietary drivers to work in Linux and sometimes the Qubes dom0 environment (the VM that acts as a bridge between the physical hardware on the machine and the virtual machines) doesn’t offer the latest support out of the box, even with more recent backported kernels, since it’s based on a somewhat older Fedora revision. This means that installing Qubes on some hardware becomes tricky, requiring you to install drivers after the fact.
The Librem 13v1 was the first hardware officially supported by the Qubes project, and since then we’ve made sure that each revision continues to work with Qubes out of the box. This includes the Librem 14, which does require the 4.0.4 or newer release of Qubes to get a recent kernel that supports the 10th generation Intel CPU. Since Librem laptops don’t require any proprietary drivers, generally speaking if the kernel is new enough to support the CPU, any Linux distribution should “just work” out of the box and Qubes is no exception. While we now offer Qubes pre-installed, at the time I received my Librem 14 we didn’t, so I just went through the standard Qubes install myself, and restored the VMs backed up from my Librem 13v4, all of which was uneventful.

Like previous laptops, the Librem 14 offers hardware kill switches to disable WiFi, and the camera and microphone. These work as expected and it’s really nice to have that LED confirmation of the switch state. I haven’t yet done anything with the new notification LED but that’s something I’d like to explore in the new year.

The new hardware Ethernet port is also a nice addition, in particular when I want to perform Qubes backups, which means transferring tens of gigabytes over the network. Because Qubes virtualizes USB devices so you can isolate them from your VMs and attach and detach them at will, using USB ethernet adapters can add an additional step, as you much manually attach it to your networking VM each time you plug it in. The Librem 14’s built-in Ethernet device was automatically detected and attached to my network VM during the install process just like my WiFi card, so I can just hotplug an Ethernet cable in and Qubes will automatically connect to the network.
Librem EC Support
One of the nice new features of the Librem 14 is that the embedded controller (which manages the keyboard along with other core computer functions) runs our free software Librem EC firmware. This not only means you can audit the firmware code, but also gives you extra control over hardware settings, such as changing your battery charging profiles. On a related note, the various hotkeys on the keyboard work the same in Qubes as they do in PureOS.
There is an additional kernel module you must use if you want access to view and to change EC settings within the OS. We include this module in PureOS, but it doesn’t come with Qubes. Fortunately it’s relatively simple to add by building and installing our dkms module. You can follow the steps here.
Hardware Performance
While the Librem 13v4 was no slouch in performance and ran Qubes well for years, the Librem 14 is in another league. With Qubes you tend to have ten or more VMs running at the same time. Many of these VMs might have duplicate versions of a resource-hungry web browser running. For instance, on any particular day my work laptop has three instances of Firefox running across three VMs. One browser is strictly for more secure sites that require a login, one browser is in my “untrusted” VM for regular web browsing, and I also have a browser running in a disposable VM for loading anything questionable, or where I want to disable third party browser security plugins entirely.
This sort of workflow where you have multiple instances of big applications each within their own VM makes heavy use of multiple cores and having a 10th generation Intel CPU with 6 cores and 12 threads, along with plenty of RAM, makes everything run really smoothly. I no longer run into the dreaded “Qubes doesn’t have enough RAM to start this VM” warnings I used to get back on 8GB of RAM. This also results in a much cooler, and therefore quieter machine. Laptop fans ramp up in response to the CPU speed, which itself ramps up to address big workloads like compiling software across multiple cores. Because the new CPU is so much faster, I find I rarely hit the kind of thresholds that trigger the CPU fan, unless I’m doing something intentionally resource-heavy like compiling PureBoot.
Video Conferencing
One particular pain point in Qubes, in general, is video conferencing. Beyond the extra steps you need to perform to connect the camera and microphone to a particular VM, joining a video conference with multiple high-definition video streams is an area where the virtualization overhead in Qubes really shows. The moment I joined a video conference on past laptops, the fan would jump to 100% as the CPU spiked. Depending on the video conference software and the number of attendees, sometimes I even experienced some lag and stuttering audio and I’d find myself disabling video to keep up.
Video conferences in Qubes on a Librem 14 is a totally different experience. I was bracing for the fan to spin up to 100% and the video to stutter but instead the video conference acted like you’d expect outside of virtualization. Video conferencing is a much more pleasurable, quieter, and full-featured experience on the Librem 14 and it’s nice to no longer have to worry about my audio stuttering.
Conclusion
I admit I had high expectations for running Qubes on the Librem 14 before I got it. After all, we did design it at least partially with running Qubes in mind. Having now used it for a number of months, I can say that it’s met and exceeded my expectations (and based on some of the feedback I’ve gotten from customers, I’m not the only one). It’s really nice to run Qubes on a machine not only with full hardware support, but also with horsepower to spare. Now that we are almost at shipping parity, and it’s a supported, pre-installed option here at Purism, if you have been curious to try Qubes out, I think the Librem 14 is the ideal platform.
Purism Products and Availability Chart
| Model | Status | Lead Time | ||
|---|---|---|---|---|
 | Librem Key (Made in USA) | In Stock ($59+) | 10 business days | |
 | Liberty Phone (Made in USA Electronics) | Available on backorder ($1,999+) 4GB/128GB | n/a | |
 | Librem 5 | In Stock ($799+) 3GB/32GB | 10 business days | |
 | Librem 11 | Out of stock | New Version in Development | |
 | Librem 14 | Out of stock | New Version in Development | |
 | Librem Mini | Out of stock | New Version in Development | |
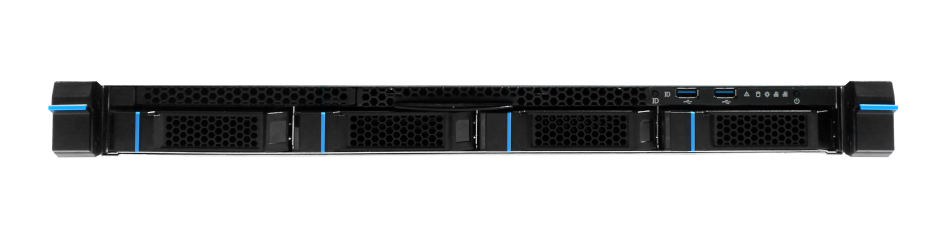
 | Librem Server | In Stock ($2,999+) | 45 business days | |
 | Librem PQC Encryptor | Available Now, contact sales@puri.sm | 90 business days | |
 | Librem PQC Comms Server | Available Now, contact sales@puri.sm | 90 business days |
Recent Posts
Related Content
- Purism’s Product Philosophy in an Age of Government–Big Tech Convergence
- PureOS Crimson Development Report: March 2026
- Wired Confirmed iPhone’s Worst-Kept Secret: Closed Systems Fail at Scale
- PureOS Crimson Development Report: January and February 2026 – Beta Released
- Privacy Under Siege


